BX is a program that is a command line tool that can generate a random seed, and then convert this into a private key. Next we can convert to a Wifi format and then a public key and a public address. You can download BX [here].
Bitcoin key generation using BX from libbitcoin |
Theory
With Bitcoin, we create a 256-bit random value for the private key and then convert it to Wallet Interchange Format key (WiF) format, which is a Base-58 form for the random key. This is the format that is stored in the Bitcoin Wallet. For example, a sample private key is:
Private key: 5c04990cf2fb95ca8749d4021100ee98b0744e81a5ec00a2177aeaf4b29c00d3
We then convert this into WiF format (Base-58) to give:
5JWp4FM7sfAAE88DW3yvGF5mQyrsEXeWzXZn79bg61Vg8YMfJjA
This can be stored in a Bitcoin wallet. Next, we can take the private key and a hash value and covert it into a useable Bitcoin address, such as:
1A3CohNBuB6kFAMtp3KFEYwv3Eu58F2HyN
≈The format of the keys is defined below, where we create a 256-bit private key and convert this to a WiF private key. Next, we generate a 512-bit public key and then take a 160-bit RIPEM-160 hash and convert it to a Bitcoin address:
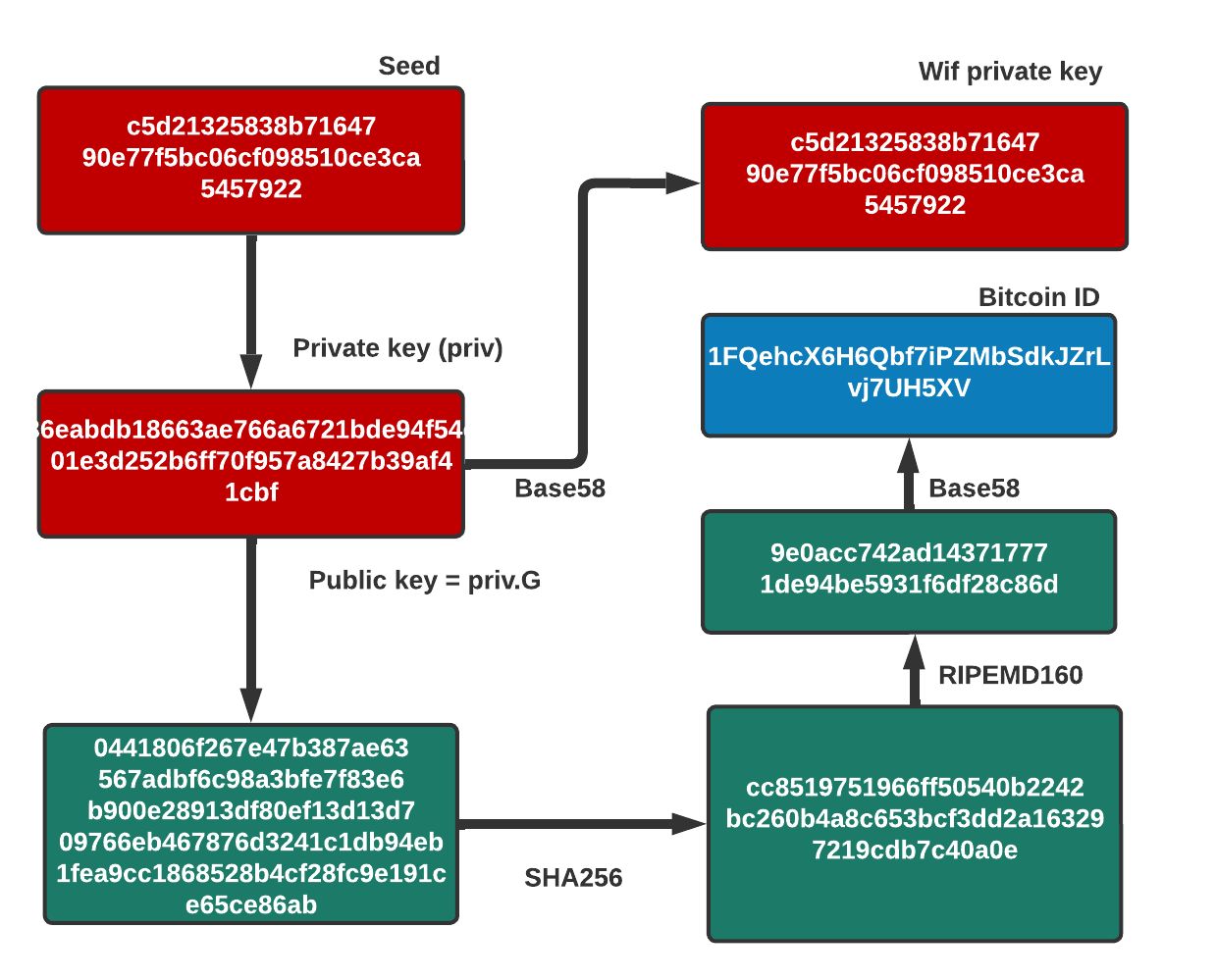
Converting from seed to address
The major problem with using bx seed is that it takes its seed value from the 32-bit system clock, and so only \(2^{32}\) seeds will be produced, and thus only \(2^{32}\) possible Bitcoin addresses. If we use a pure random number, we would have \(2^{256}\) different seed values, and which would be almost impossible to search through. But, with bx seed, we only have \(2^{32}\) — which is relatively easy.
We can then easily write a PowerShell script to go through possible seed values and discover the associated private key, the public key, and the Bitcoin address:
$seed = bx seed "Seed: ",$seed $pri = bx ec-new $seed " `nEC private key: ",$pri $mn =bx mnemonic-new $seed "`nMnemonic: ",$mn $wif = bx ec-to-wif $pri " `nWif: ",$wif $pub = bx ec-to-public $pri " `nPublic key: ",$pub $add = bx ec-to-address $pub " `nBitcoin address: ",$add
A sample run gives:
Seed: 313dd7017988f73e8869008c2ac28e390094bc85208adde3 EC private key: 7173fc4e3bf366417d163dd936eefc29117fd1cc78a540f0a3c38b19d55f006d Mnemonic: couple upgrade scare vessel month palm canvas cactus method figure phone improve announce furnace behind bacon target bonus Wif: L12FPHg9UmzEgSJ1uj7pHxzjDQirERTZX3dSFLjVFdV8ovZJUnro Public key: 021ac378f7738efb40216f014e4eb347ee28823a7e8d8c00624b53c6ce87b0246c Bitcoin address: 1HXeUdHCk2FnHf9Q3toqoxQKXngJVZACAL
In this case, we start with a seed of “313dd7017988f7 … 094bc85208adde3”, and then can generate a new 256-bit private key of “7173fc4e3bf366 … c38b19d55f006d”. If we need a mnemonic version of the private key to write down, we can see it is “couple upgrade scare vessel month palm canvas cactus method figure phone improve announce furnace behind bacon target bonus”. It can then be converted into a Wif format of “L12FPHg9Um … SFLjVFdV8ovZJUnro”. Next, we generate the public key of “021ac378f7738 … 3c6ce87b0246c”. In this case, we have a compressed public key point, and is the x-axis point, and a “02” if the y-point is even, or a “03” if the point is odd. If we try another key, we get an odd y-axis point:
Public key: 036ba64d0a2ea6d187da00262b819b44f78ceaae757ef90dead3c141e57e84deb4
And, so, up to this point, we have gathered the seed, the private key, the Wif, and the public key. It is now simple to take the public key and convert it into a Bitcoin ID. In this case, we have an ID of “1HXeUd … KXngJVZACAL”. Once this is discovered, an intruder would then be able to link it with the associated private, and sign-off a transaction.
Coding
The following defines the coding:
echo Seed bx seed echo EC private key bx seed | bx ec-new echo Mnemonic bx seed | bx mnemonic-new echo Wif bx seed | bx ec-new | bx ec-to-wif echo Public key bx seed | bx ec-new | bx ec-to-public echo Bitcoin address bx seed | bx ec-new | bx ec-to-public | bx ec-to-address
In Powershell, we have:
$seed = bx seed "Seed: ",$seed $pri = bx ec-new $seed " `nEC private key: ",$pri $mn =bx mnemonic-new $seed "`nMnemonic: ",$mn $wif = bx ec-to-wif $pri " `nWif: ",$wif $pub = bx ec-to-public $pri " `nPublic key: ",$pub $add = bx ec-to-address $pub " `nBitcoin address: ",$add
A sample run is:
Code: b8a7b321e5b5fb31e6e27e21cfb48152100f934e99fdbc6f EC private key: 963319370381a054e9c38db5cbc7f8d1a669b6b1fcf5bc857fba03fd41ee7137 Mnemonic: reward diesel silent slice garden ocean oppose exist canyon laundry cake picnic abstract situate denial distance round kidney Wif: L2FgMMyD7FAwzAKntRpBbhH3xY8k63doqFdS8eXYVEfumAdpUvXu Public key: 039e3d7a15bb586ad002baeabcf213565d26d7a86d35a77c1a5fe2fd6ddad613eb Bitcoin address: 1HveHos4rtsVmSRTRU6TDSJyyRVtPK8Hxe
A help page is:
Usage: bx COMMAND [--help] Version: 3.2.0 Info: The bx commands are: address-decode address-embed address-encode base16-decode base16-encode base58-decode base58-encode base58check-decode base58check-encode base64-decode base64-encode bitcoin160 bitcoin256 btc-to-satoshi cert-new cert-public ec-add ec-add-secrets ec-multiply ec-multiply-secrets ec-new ec-to-address ec-to-ek ec-to-public ec-to-wif ek-address ek-new ek-public ek-public-to-address ek-public-to-ec ek-to-address ek-to-ec fetch-balance fetch-header fetch-height fetch-history fetch-public-key fetch-stealth fetch-tx fetch-tx-index fetch-utxo hd-new hd-private hd-public hd-to-ec hd-to-public help input-set input-sign input-validate message-sign message-validate mnemonic-new mnemonic-to-seed qrcode ripemd160 satoshi-to-btc script-decode script-encode script-to-address seed send-tx send-tx-node send-tx-p2p settings sha160 sha256 sha512 stealth-decode stealth-encode stealth-public stealth-secret stealth-shared token-new tx-decode tx-encode tx-sign uri-decode uri-encode validate-tx watch-address watch-stealth watch-tx wif-to-ec wif-to-public wrap-decode wrap-encode Bitcoin Explorer home page: https://github.com/libbitcoin/libbitcoin-explorer
Elliptic Curve
Bitcoins use Elliptic Curve Ciphers (ECC) with a 256-bit private key (and a 512-bit public key). If you want to know more about ECCs, there is an outline here:
 [
[