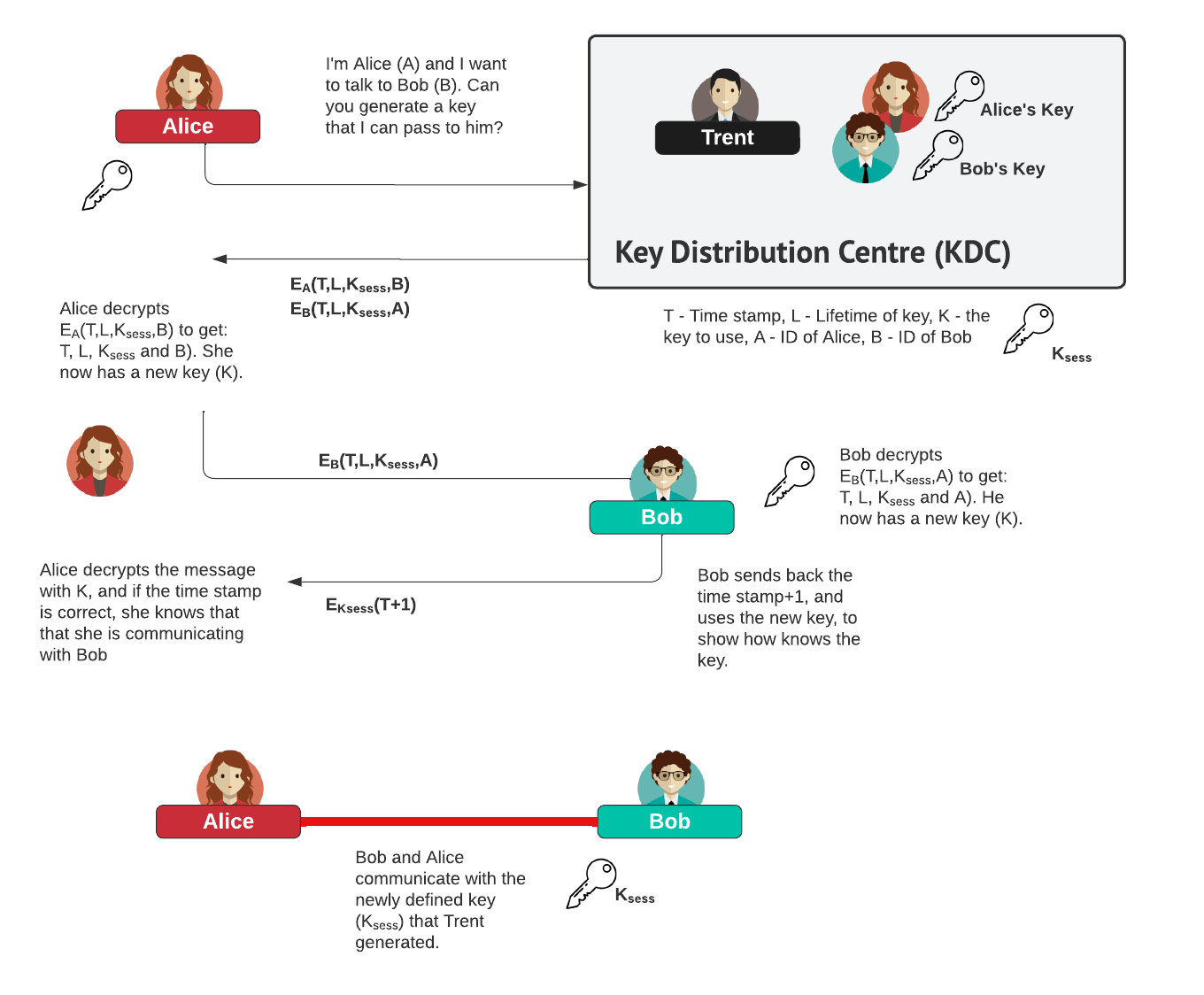
Kerberos ExampleKerberos is used to share a session key between Bob and Alice, and uses Trent to generate the key. First we determine the ID for Alice, Bob, and key to be used by Alice to communicate with Trent, and for Bob to communciate with Trent: Now Trent calculates a timestamp, a Life Time (L), a random session key (K) and Bob's identity (B), and encrypts with Alice's Key:
Next Alice can now decrypt the first part (EA(T,L,K,B)) as she has the encryption key for this. She can then determine the session key (K). Next she encrypts her identity (A) and the timestamp (T) with the session key (EK) and sends to Bob:
Bob can now decrypt EB(T,L,K,A) with EB, and will thus determine K (which is the session key). After this he can then decrypt EK(A,T), to determine Alice's identity (A) and the Timestamp (T). He will then increment the T stamp by one, and encrypt with the session key and send back to Alice:
Alice will then receive this, and decrypt with the session key EK, and determine that it has the correct time stamp, and thus proves that Bob has sent it back. Alice and Bob now have a shared key, and can now use it to send encrypted content. |
Presentation
Explanation
So let's relate this to real life. Bob and Alice trust Trent, but want a way to identify each other and communicate in a secret way. So Alice goes to Trent and says that she has to prove her identity to Bob, and vice-versa. For this Trent will make a special key for a box, and will make a copy for Bob and Alice (he might also keep a copy for himself, just in case they lose them). Trent will then take a photograph of Alice, and write down the date and time on it, and the amount of time he can verify Alice for. He will then put it into the box, and gives the box to Alice, along with the key. Along with this he will give her a sealed letter for the attention Bob which has his stamp on it. Inside will be a photograph of Alice that he took, and the secret key, along with the date/time that he created the key.
Alice goes home, and then puts her photograph in the box, and locks it with the secret key. She then passes the box, without the key, along with the sealed letter to Bob. Bob opens the sealed letter, which has a key inside to open up the box, and which has the photograph that Trent took of Alice. Bob then opens the box with the secret key provided by Trent, and takes out the photograph that Alice has provided. If it is the same as the one that Trent put in the sealed letter, Bob thus verifies Alice's identity.
Bob and Alice now have the same key to open and close the secret box, and can now use it to send secret messages to each other. No-one else will have that unique key, thus any messages in there must have been provided by Bob and Alice.
Theory
The steps are:
Step 1: First Alice and Bob send their identity to Trent, who will then find the keys where relate to them.
Step 2: Next Trent creates a random key to be used for the session key, and create a Timestamp (\(T\)), a Lifetime (\(L\)), which define the starting time for the trust relationship, and how long it will be valid for. He will then create two parts to send back to Alice:
\(E_A(T,L,K,B)\) and \(E_B(T,L,K,A)\)
where is the first part is encrypted with Alice's secret key, and the other part is encrypted with Bob's secret key.
Step 3: Next Alice will decrypt the first part, and can thus determine \(T\) (the timestamp), \(L \) (the lifetime), \(K\) (the session key) and \(B\) (Bob's Identity). Alice now knows the session key (K), and now uses it to encrypt the Timestamp (T) and Alice's Identity (A) to Bob, along with the second part of the message from Trent [\(E_B(T,L,K,A)\)]:
\(E_K(T,A)\) and \(E_B(T,L,K,A)\)
Step 4: Bob will then decrypt the second part, and determines the session key (\(K\)), which can be used to decrypt the first part. He will then check Alice's identity is the same as the one that Trent sent.
Step 5: Bob takes the time stamp and add one onto it, and sends back to Alice:
\(E_K(T+1)\)
Step 6: Alice then decrypts with the session key, and checks the timestamp. If it checks with the expected value, then Bob has proven his identity. Bob and Alice and now communicate using the session key, and be secure, as only Trent will know the session key.
Coding
The C# coding is:
using System;
using System.Collections.Generic;
using System.Security.Cryptography;
using System.Text;
using System.IO;
class ker
{
static void Main(string[] args)
{
Aes myAes = Aes.Create();
byte[] keyAlice = myAes.Key;
byte[] keyAliceIV = myAes.IV;
string keya = ByteArrayToHexstring(myAes.Key);
myAes = Aes.Create();
byte[] keyBob = myAes.Key;
byte[] keyBobIV = myAes.IV;
string keyb = ByteArrayToHexstring(myAes.Key);
string bobID = "Bob";
string aliceID = "Alice";
string bob = "Bob";
string alice = "Alice";
myAes = Aes.Create();
byte[] session = myAes.Key;
byte[] sessionIV = myAes.IV;
string Kab = ByteArrayToHexstring(session);
DateTime timestamp = DateTime.UtcNow;
DateTime timestamp2 = DateTime.UtcNow.AddSeconds(1);
int lifetime = 100;
bob = bobID;
alice = aliceID;
byte[] encrypted1 = EncryptstringToBytes_Aes(bobID, session, sessionIV);
byte[] encrypted2 = EncryptstringToBytes_Aes(aliceID, keyBob, keyBobIV);
byte[] encrypted3 = EncryptstringToBytes_Aes(aliceID + bobID, keyAlice, keyAliceIV);
byte[] encrypted4 = EncryptstringToBytes_Aes(bobID + aliceID, session, sessionIV);
string part1 = ByteArrayToHexstring(encrypted1) + "," + ByteArrayToHexstring(encrypted2);
string part2 = ByteArrayToHexstring(encrypted3) + "," + ByteArrayToHexstring(encrypted2);
string part3= ByteArrayToHexstring(encrypted4);
Console.WriteLine("BobID: %s",bobID);
Console.WriteLine("AliceID: %s",aliceID);
Console.WriteLine("Keya: %s",keya);
Console.WriteLine("Keyb: %s",keyb);
Console.WriteLine("Trent sends to Alice: %s",part1);
Console.WriteLine("Alice sends to Bob: %s",part2);
Console.WriteLine("Bob sends to Alice: %s",part3);
}
static byte[] stringToByteArray(string str)
{
UTF8Encoding encoding = new UTF8Encoding();
return encoding.GetBytes(str);
}
string ByteArrayToString(byte[] input)
{
UTF8Encoding enc = new UTF8Encoding();
string str = enc.GetString(input);
return str;
}
static string ByteArrayToHexstring(byte[] ba)
{
StringBuilder hex = new StringBuilder(ba.Length * 2);
foreach (byte b in ba)
hex.AppendFormat("{0:x2}", b);
return hex.ToString();
}
static byte[] EncryptstringToBytes_Aes(string plainText, byte[] Key,
byte[] IV)
{
if (plainText == null || plainText.Length <= 0)
throw new ArgumentNullException("plainText");
if (Key == null || Key.Length <= 0)
throw new ArgumentNullException("Key");
if (IV == null || IV.Length <= 0)
throw new ArgumentNullException("Key");
byte[] encrypted;
// Create an Aes object
// with the specified key and IV.
using (Aes aesAlg = Aes.Create())
{
aesAlg.Key = Key;
aesAlg.IV = IV;
// Create a decrytor to perform the stream transform.
ICryptoTransform encryptor = aesAlg.CreateEncryptor(aesAlg.Key
, aesAlg.IV);
// Create the streams used for encryption.
using (MemoryStream msEncrypt = new MemoryStream())
{
using (CryptoStream csEncrypt = new CryptoStream(msEncrypt
, encryptor, CryptoStreamMode.Write))
{
using (StreamWriter swEncrypt = new StreamWriter(
csEncrypt))
{
//Write all data to the stream.
swEncrypt.Write(plainText);
}
encrypted = msEncrypt.ToArray();
}
}
}
// Return the encrypted bytes from the memory stream.
return encrypted;
}
}