Ahmad-Afzal-Iqbal (AAI) signcryption with GolangNormally when we digitally sign something, we have to create a hash of the data, and then use the public key of the recipient to encrypt it. With signcryption we sign something at the same time as encrypting it. Ahmad-Afzal-Iqbal (AAI) [1] encryption implements signcryption using elliptic curves and is designed for Alice to send a signature to a firewall in order for it to check the signature. If valid, the firewall validates the signencryption cipher to Bob. The firewall never has to see the cipher text (\(C\)) and only works on (\(R,S\)). This means that the firewall never has to view the ciphertext, in order to determine if the signature is correct for the message. |
Outline
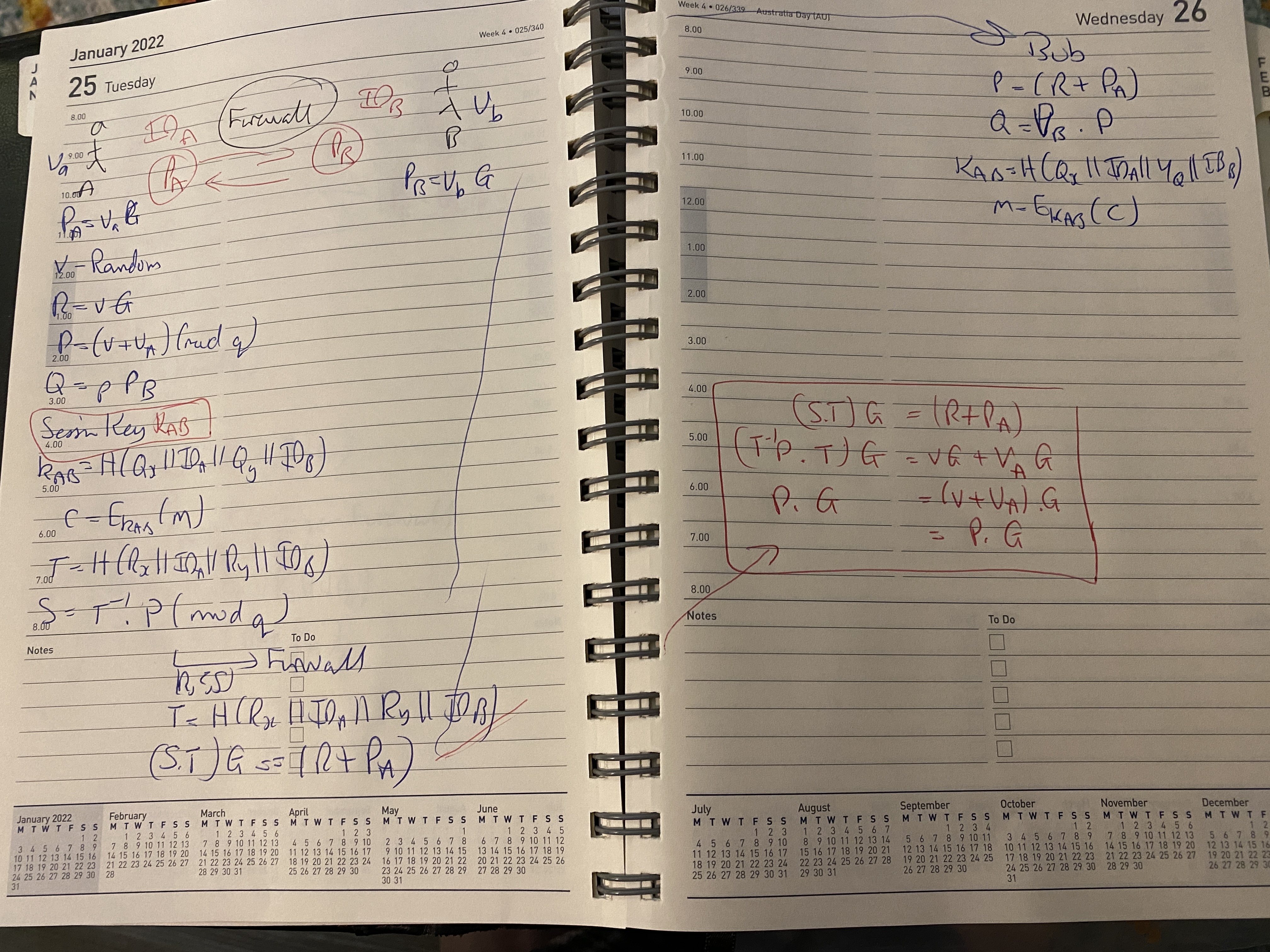
Initially Bob and Alice create their public keys as randon 256-bit values: \(v_A\) and \(v_B\), and with public keys of:
\(P_A=v_A.G\)
\(P_B=v_B.G\)
Bob and Alice then create a one-time session key: \(K_{AB}\). First Alice generates a random value of \(v\) and then computes:
\(R=v.G\)
\(P=(v+v_A) \pmod q\)
\(Q=P.P_B\)
and where \(q\) is the order of the curve. The session key (\(K_{AB}\)) is then generated with:
\(K_{AB} = H(Q_x || ID_A || Q_y || ID_B)\)
and where \(Q_x\) is the \(x\) co-ordinate of \(Q\) and \(Q_y\) is the y co-ordinate of \(Q\). The "||" operator defines a concatenation of the byte values. Alice then encrypts a message (\(m\)) using the session key:
\(C=E_{K_{AB}}(m)\)
Also:
\(T=H(R_x || ID_A || R_y || ID_B)\)
And the signature is:
\(S=T^{-1}.P \pmod q\)
Alice will send the signcryption of \((R,C,S)\) to Bob. The firewall picks this up and computes:
\(T=H(R_x || ID_A || R_y || ID_B)\)
The firewall then verifies that:
\((ST).G = (R+P_A)\)
If true, the firewall will forward \((R,C,S)\) to Bob. Bob then computes the session key from:
\(P=(R+P_A)\)
\(Q=v_B.P\)
The session key is then:
\(K_{AB} = H(Q_x || ID_A || Q_y || ID_B)\)
\(m=E_{K_{AB}}(C)\)
An outline is:
Code
The code is:
package main
import (
"encoding/base64"
"fmt"
"io"
"math/rand"
"os"
"github.com/DavidHuie/signcryption"
"github.com/DavidHuie/signcryption/aai"
)
func toBase64(in []byte) string {
return base64.StdEncoding.EncodeToString(in)
}
func genCert(rand io.Reader) *signcryption.Certificate {
cert, _ := signcryption.GenerateCertificate(rand)
cert.ID = make([]byte, 16)
_, _ = io.ReadFull(rand, cert.ID)
return cert
}
func main() {
msg := "This is a test"
ad := "And some additional data."
argCount := len(os.Args[1:])
if argCount > 0 {
msg = os.Args[1]
}
if argCount > 1 {
ad = os.Args[2]
}
rand := rand.New(rand.NewSource(0))
sc := aai.NewP256()
source, dest := genCert(rand), genCert(rand)
output, _ := sc.Signcrypt(source, dest, []byte(msg), []byte(ad))
fmt.Printf("Message: %s\n", msg)
fmt.Printf("Additional data: %s\n", ad)
fmt.Printf("\nCipher text: %x\n", output.Ciphertext)
fmt.Printf(" Cipher text: %s\n", toBase64(output.Ciphertext))
fmt.Printf("R: %x\n", output.R)
fmt.Printf(" R: %s\n", toBase64(output.R))
fmt.Printf("R: %x\n", output.Signature)
fmt.Printf(" R: %s\n", toBase64(output.Signature))
valid, _ := sc.Verify(source, dest, []byte(ad), output)
if valid {
fmt.Printf("Signature is valid\n")
}
plaintextCandidate, valid, _ := sc.Unsigncrypt(source, dest, []byte(ad), output)
if valid {
fmt.Printf("Plaintext: %s", plaintextCandidate)
}
}
A sample run is:
Message: Hello. How are you? Additional data: Additional data Cipher text: 5bf55b67c1303d6278f6b60c6ce20d5dc96fede6e6b70d49da020341bb04d61b4d1e40 Cipher text: W/VbZ8EwPWJ49rYMbOINXclv7ebmtw1J2gIDQbsE1htNHkA= R: 04041ecba5c76424828aa8c71ed068055114281d0ae7bce760a544fafedc4de3752bd149f3fa6ec099649d42bfa4b0f5056ff586aa9546b8df3a729f2681c7338d R: BAQey6XHZCSCiqjHHtBoBVEUKB0K57znYKVE+v7cTeN1K9FJ8/puwJlknUK/pLD1BW/1hqqVRrjfOnKfJoHHM40= S: 3f04cb8ea76cef977d0f4da1e2eb1176160b50e67281de01cb99bad10e01e152 S: PwTLjqds75d9D02h4usRdhYLUOZygd4By5m60Q4B4VI= Signature is valid Plaintext: Hello. How are you?
Reference
[1] Iqbal, W., Afzal, M., & Ahmad, F. (2013, December). An efficient elliptic curve based signcryption scheme for firewalls. In 2013 2nd National Conference on Information Assurance (NCIA) (pp. 67-72). IEEE [here].
 [
[