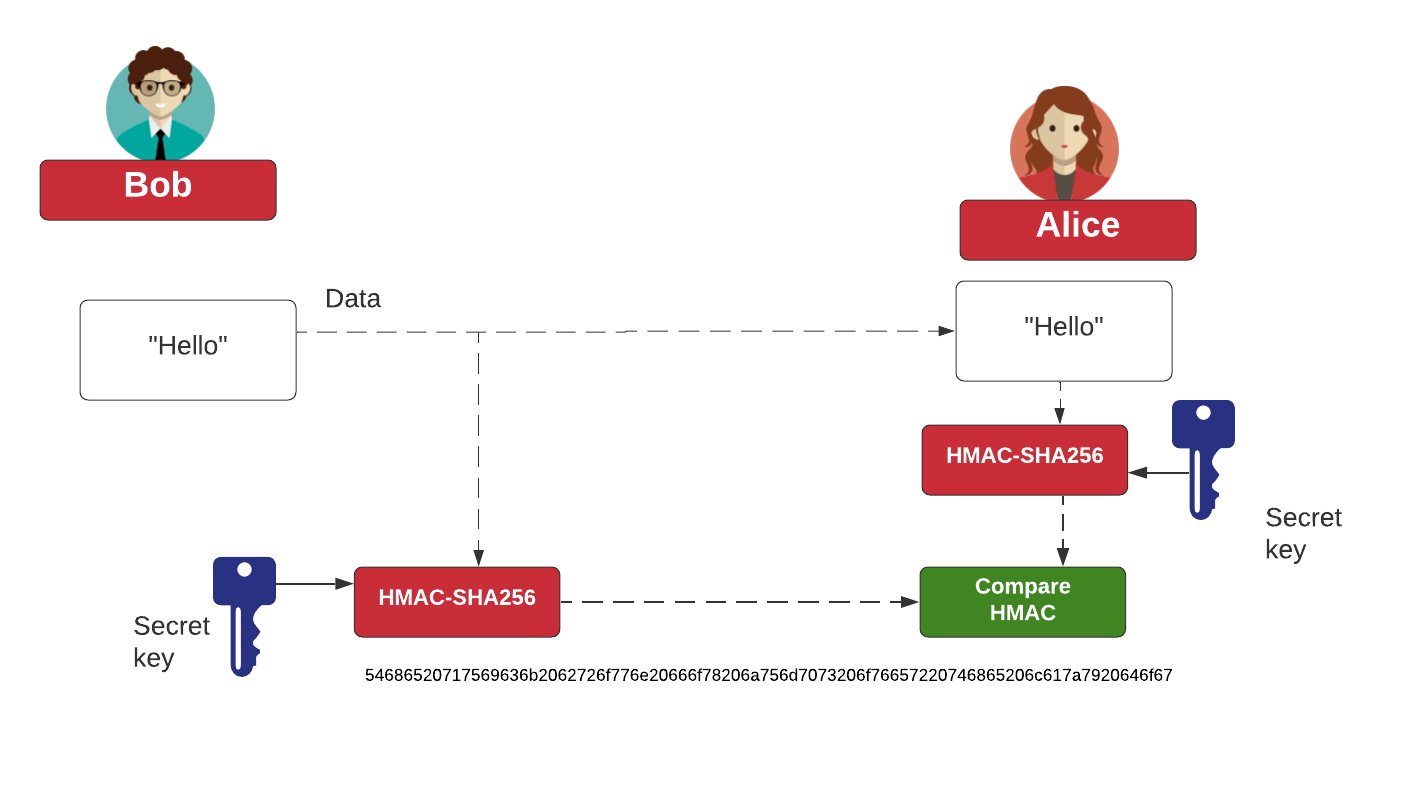
HMAC is a message authentication code (MAC) that can be used to verify the integrity and authentication of a message. It involves hashing the message with a secret key and thus differs from standard hashing, which is purely a one-way function. As with any MAC, it can be used with a standard hash function, such as MD5 or SHA-1, which results in methods such as HMAC-MD5 or HMAC-SHA-1. Also, as with any hashing function, the strength depends on the quality of the hashing function, and the resulting number of hash code bits. Along with this, the number of bits in the secret key is a factor in the strength of the hash. The figure below outlines the operation, where the message to be sent is converted with a secret key, and the hashing function, to an HMAC code. This is then sent with the message. On receipt, the receiver recalculates the HMAC code from the same secret key, and the message, and checks it against the received version. If they match, it validates both the sender and the message. In this case we will implement for HMAC-MD5, HMAC-SHA1, HMAC-SHA256, HMAC-SHA384 and HMAC-SHA512
HMAC with PowerShell |
Method
HMAC is a message authentication code (MAC) that can be used to verify the integrity and authentication of a message. It involves hashing the message with a secret key and thus differs from standard hashing, which is purely a one-way function. As with any MAC, it can be used with a standard hash function, such as MD5 or SHA-1, which results in methods such as HMAC-MD5 or HMAC-SHA-1. Also, as with any hashing function, the strength depends on the quality of the hashing function, and the resulting number of hash code bits. Along with this, the number of bits in the secret key is a factor in the strength of the hash. The figure below outlines the operation, where the message to be sent is converted with a secret key, and the hashing function, to an HMAC code. This is then sent with the message. On receipt, the receiver recalculates the HMAC code from the same secret key, and the message, and checks it against the received version. If they match, it validates both the sender and the message.
Coding
$word=$Args[0] $secret=$Args[1] "Input word: "+$word "Secret: "+$secret $hmacsha = New-Object System.Security.Cryptography.HMACMD5 $hmacsha.key = [Text.Encoding]::ASCII.GetBytes($secret) $hash1=$hmacsha.ComputeHash([System.Text.Encoding]::UTF8.GetBytes($word)) "`nHMAC-MD5: " + [Convert]::ToBase64String($hash1) "HMAC-MD5: " + [Convert]::ToHexString($hash1) $hmacsha = New-Object System.Security.Cryptography.HMACSHA1 $hmacsha.key = [Text.Encoding]::ASCII.GetBytes($secret) $hash1=$hmacsha.ComputeHash([System.Text.Encoding]::UTF8.GetBytes($word)) "`nHMAC-SHA1: " + [Convert]::ToBase64String($hash1) "HMAC-SHA1: " + [Convert]::ToHexString($hash1) $hmacsha = New-Object System.Security.Cryptography.HMACSHA256 $hmacsha.key = [Text.Encoding]::ASCII.GetBytes($secret) $hash1=$hmacsha.ComputeHash([System.Text.Encoding]::UTF8.GetBytes($word)) "`nHMAC-SHA256: " + [Convert]::ToBase64String($hash1) "HMAC-SHA256: " + [Convert]::ToHexString($hash1) $hmacsha = New-Object System.Security.Cryptography.HMACSHA384 $hmacsha.key = [Text.Encoding]::ASCII.GetBytes($secret) $hash1=$hmacsha.ComputeHash([System.Text.Encoding]::UTF8.GetBytes($word)) "`nHMAC-SHA384: " + [Convert]::ToBase64String($hash1) "HMACSHA384: " + [Convert]::ToHexString($hash1) $hmacsha = New-Object System.Security.Cryptography.HMACSHA512 $hmacsha.key = [Text.Encoding]::ASCII.GetBytes($secret) $hash1=$hmacsha.ComputeHash([System.Text.Encoding]::UTF8.GetBytes($word)) "`nHMAC-SHA512: " + [Convert]::ToBase64String($hash1) "HMAC-SHA512: " + [Convert]::ToHexString($hash1)
A sample run shows:
Input word: message Secret: secret HMACMD5: fg0HZ3dTEhVLoW/Tr5dxog== HMACMD5: 7E0D0767775312154BA16FD3AF9771A2 HMACSHA1: DK9kn+7klT2Hv5A6wRdsReAo3xY= HMACSHA1: 0CAF649FEEE4953D87BF903AC1176C45E028DF16 HMACSHA256: i19IcCmVwVmMVz2x4hhmqbgl1KeU0WnXBgoDYFeWNgs= HMACSHA256: 8B5F48702995C1598C573DB1E21866A9B825D4A794D169D7060A03605796360B HMACSHA384: rQ706A2kJ7KjPURXyXK/dZ9Qdm+7ZlaQ1Qt8s43VIX21Wck+p8vuSOKuGltKr9NL HMACSHA384: AD0EF4E80DA427B2A33D4457C972BF759F50766FBB665690D50B7CB38DD5217DB559C93EA7CBEE48E2AE1A5B4AAFD34B HMACSHA512: G7pYfHMO7box9Tq7C2ylieCd5OiU7kVeYUCAc5l1mtqvoGnux8AWR7sXPcsX9V0ir0mhgHG3SMXC7df3qCnGMg== HMACSHA512: 1BBA587C730EEDBA31F53ABB0B6CA589E09DE4E894EE455E6140807399759ADAAFA069EEC7C01647BB173DCB17F55D22AF49A18071B748C5C2EDD7F7A829C632
 [
[