AES (Advanced Encryption Standard)
With symmetric key, we use the same key to encrypt and to decrypt. The most popular symmetric key methods are AES and ChaCha20. In its pursest form, AES is a block cipher, with 128-bit block sizes. ChaCha20 is a stream cipher. With a block cipher we need padding, and there is no padding required for a stream cipher. The main modes that we get with symmetric key are ECB (Electronic Code Book), CBC (Cipher Block Chain), CTR (Counter) and GCM (Galois Counter Mode), and with either a 128-bit, a 192-bit or a 256-bit encryption key. With symmetric key we can also use AEAD (Authenticated Encryption with Associated Data), and which allows additional data to be added into the cipher, and which can then be used to authenticate it. This additional data might relate to a session number.
|
Outline
With symmetric key encryption, we use the same key to encrypt and decrypt:

Alice creates a secret message and ciphers it with her secret key, and then sends this to Bob. He also has the secret key, and so he decrypts it and reveals the secret message. It says “You can take tomorrow as a holiday”. Bob is happy and takes the holiday. Eve, though, has been listening to their communications, and, the next day, resends the ciphered message, even though she cannot read it. Bob takes the next day off, and Alice wonders why he is not at work? Eve has thus performed a replay attack on Alice’s ciphered message. So what we need is to bind the cipher to a network connection or a session, in order that Eve cannot recreate the same scenario.
With enhanced encryption methods, we can both authenticate the cipher and prove its integrity. This is known as Authenticated Encryption with Associated Data (AEAD). For this we provide additional data to authenticate the encryption process, and where we can identify where the ciphertext has been modified, and for it not to be decrypted.
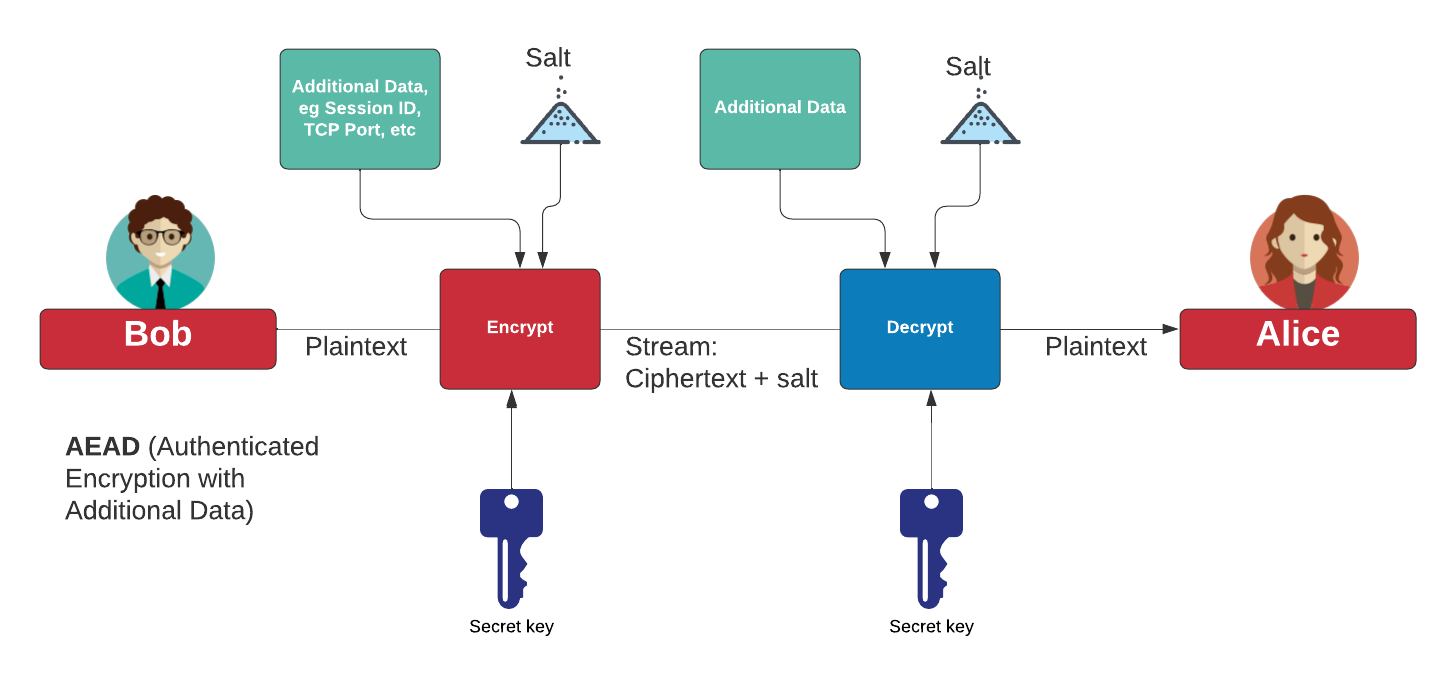
With most conventional AEAD methods we create a nonce value and add additional data (AD) that is authenticated but not encrypted. The additional data can include:
addresses, ports, sequence numbers, protocol version numbers, and other fields that indicate how the plaintext or ciphertext should be handled, forwarded, or processed
In this way, we can bind network packets to the encrypted data, and provide integrity, so that an intruder cannot copy and paste valid ciphertext from other transmissions. For example, if we bind to a packet sequence number and the port, the authentication would fail for another sequence number or another port.
The main methods we can use for AEAD are AES GCM, AES SIV, AES CCM, ChaCha20/Poly1305 and AES OCB3. These will be explained in the following sections.
Presentation

 [
[
