2. Symmetric Key [Home] The key concepts are:
What you should know at the end of unit?
Presentations
Tests
AddendumIn the lecture, at the end of Unit 2 (Symmetric Key) the table should be: 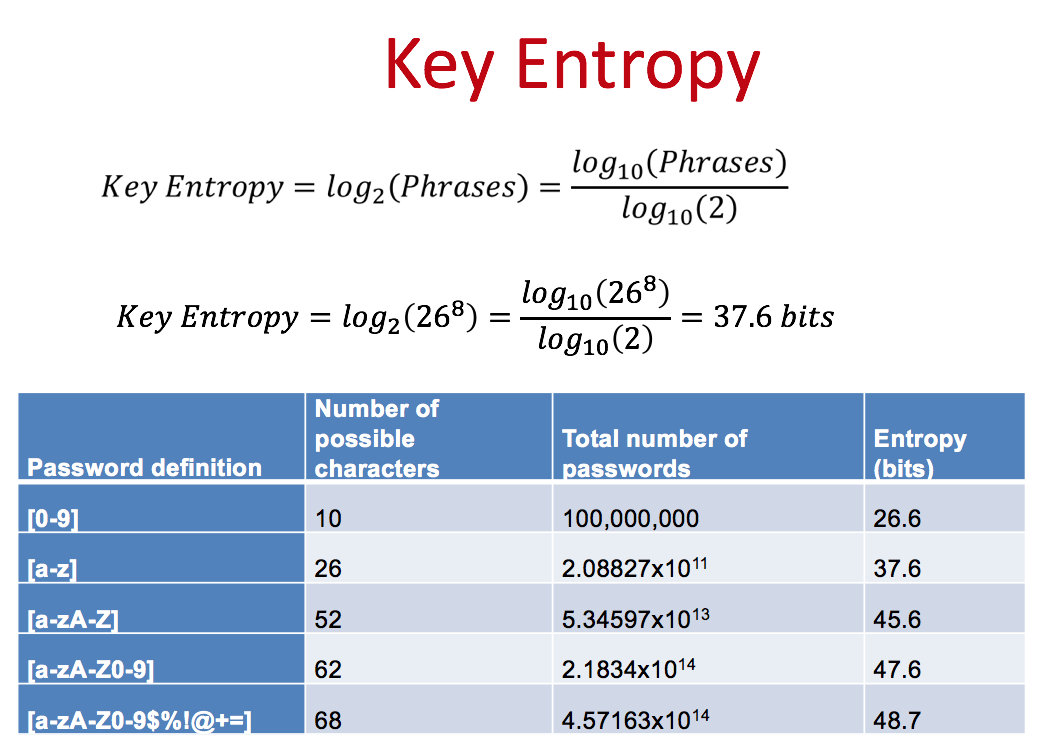
The text from the book on Page 83: Now, we can use key entropy which will determine the equivalent key size for the limited range of key. Key Entropy\(=log_2(Phrases)=\frac{log_{10} (Phrases)}{log_{10} (2)}\) For our 8 character passwords, we can determine the equivalent key size of: Key Entropy\(=log_2(26^8)=\frac{log_{10}(26^8)}{log_{10}(2)}=37.6\) bits Thus if we are using a 128-bit encryption key, we are not using an equivalent of 50 bits, which considerably reduces the strength of the encryption process. Quick demosInterested in knowing more?Any questions?Contact Bill Skype: billatnapier Links
|