With the Diffie-Hellman (DH) we use the form of \(g^x \pmod p\), and where \(g\) is the generator and \(p\) is a large prime number. In order to implement DH, we create either a generator value of 2, 3 or 5, and then select a prime number which works with this generator value. In real-life we would generate a prime number of at least 2,048 bits. A command of "openssl dhparam -2 512" creates a random prime number with 512 bits and which works with a generator of \(g=2\).
Generate Diffie Hellman parameters with OpenSSL |
Outline
The Diffie-Hellman (DH) method is perhaps one of the greatest inventions in Cybersecurity, and was created by Whitfield Diffie and Marty Hellman. With the DH method, Bob creates a random value (\(b\)) and Alice also creates a random value (\(a\)). Next Bob computes \(B=g^b \pmod p\) and sends it to Alice. Alice computes \(A=g^a \pmod p\) and sends this to Bob. Bob raises the value of \(A\) to the power of \(b\) and takes \(\pmod p\), and Alice raises \(B\) to the power of \(a\) and takes \(\pmod p\). In the end, they will have the same shared value: \(g^{ab} \pmod p\). This can then be used to derive an encryption key that they can use for a secure tunnel (Figure 1). Overall, \(p\) is the large prime number, and also known as the shared modulus between Bob and Alice.
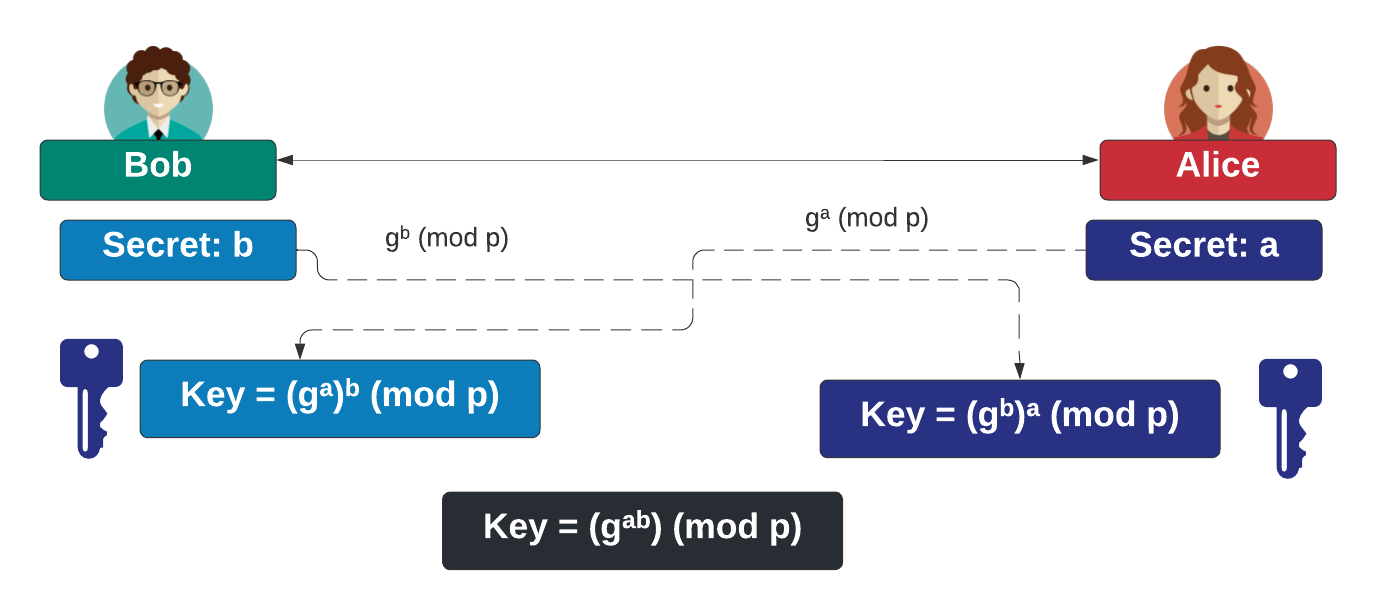
Figure 1
In the paper "Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice", the authors defines a range of prime numbers which are used for TLS key exchange for Diffie-Hellman key exchange. If these are used, then an adversory can compile a list of keys for a range of random values (a and b), and then match these. This vulnerability was given the name of Logjam.
In order to avoid Logjam, a system should be setup with a random prime number. This can be achieved with OpenSSL. For "openssl dhparam -text -2 512", we get a 512-bit prime number, and using g=2:
$ openssl dhparam -text -2 512
DH Parameters: (512 bit)
P:
00:f8:aa:01:d2:7d:e4:e4:bc:2f:ef:a6:7b:c3:fd:
06:aa:10:4f:a1:ca:0a:09:68:fd:80:49:d6:39:0a:
99:1a:eb:48:48:a4:40:31:6a:0c:34:2e:4e:a0:cf:
6a:ae:21:66:ba:aa:7a:4b:cd:18:42:76:15:7f:20:
d5:14:43:cf:7f
G: 2 (0x2)
-----BEGIN DH PARAMETERS-----
MEYCQQD4qgHSfeTkvC/vpnvD/QaqEE+hygoJaP2ASdY5Cpka60hIpEAxagw0Lk6g
z2quIWa6qnpLzRhCdhV/INUUQ89/AgEC
-----END DH PARAMETERS-----
For "openssl dhparam -text -2 1024", we get a 1024-bit prime number, and using g=2:
$ openssl dhparam -text -2 512
DH Parameters: (1024 bit)
P:
00:8b:9b:88:28:e9:71:95:36:6b:a3:6f:a5:71:21:
b7:ca:bc:3c:1e:db:24:e4:d3:f4:b8:df:d3:97:25:
e9:fa:9c:88:89:c8:d1:f3:6c:40:2c:1f:d5:66:8a:
42:b4:2f:95:f8:33:43:43:a2:57:dd:9f:5a:b7:b5:
f7:b4:b2:9c:ca:eb:61:4a:99:49:71:c5:71:0a:bb:
ce:03:6e:02:9e:16:02:ae:5f:14:54:47:dc:78:a0:
36:cf:b4:bb:83:4a:36:fc:18:b1:79:a3:a2:c1:c4:
e5:ea:4d:4d:c2:75:13:cf:df:8f:c0:6c:58:96:ea:
2f:a9:a6:11:6f:42:a5:92:97
G: 2 (0x2)
-----BEGIN DH PARAMETERS-----
MIGHAoGBAIubiCjpcZU2a6NvpXEht8q8PB7bJOTT9Ljf05cl6fqciInI0fNsQCwf
1WaKQrQvlfgzQ0OiV92fWre197SynMrrYUqZSXHFcQq7zgNuAp4WAq5fFFRH3Hig
Ns+0u4NKNvwYsXmjosHE5epNTcJ1E8/fj8BsWJbqL6mmEW9CpZKXAgEC
-----END DH PARAMETERS-----
For "openssl dhparam -text -5 768", we get a 768-bit prime number, and using g=5:
$ openssl dhparam -text -5 768
DH Parameters: (768 bit)
P:
00:bf:aa:af:b7:00:05:ca:a0:2b:fd:df:db:44:ed:
52:29:32:96:25:a5:0f:bd:ab:1a:4e:6b:fc:e1:15:
71:2c:5b:d5:4a:42:48:f9:a0:1c:b1:77:2f:8e:de:
4b:6a:14:f1:11:88:02:c3:86:10:92:f1:8b:1b:1a:
5a:58:f3:ec:6e:a6:8f:5e:77:64:d2:ca:f0:34:a5:
9b:55:f4:37:74:03:9e:89:64:c9:1a:ee:88:fc:27:
65:2b:9f:d7:5c:48:a7
G: 2 (0x2)
-----BEGIN DH PARAMETERS-----
MGYCYQC/qq+3AAXKoCv939tE7VIpMpYlpQ+9qxpOa/zhFXEsW9VKQkj5oByxdy+O
3ktqFPERiALDhhCS8YsbGlpY8+xupo9ed2TSyvA0pZtV9Dd0A56JZMka7oj8J2Ur
n9dcSKcCAQI=
-----END DH PARAMETERS----
The PEM part of the parameters is:
-----BEGIN DH PARAMETERS----- MGYCYQC/qq+3AAXKoCv939tE7VIpMpYlpQ+9qxpOa/zhFXEsW9VKQkj5oByxdy+O 3ktqFPERiALDhhCS8YsbGlpY8+xupo9ed2TSyvA0pZtV9Dd0A56JZMka7oj8J2Ur n9dcSKcCAQI= -----END DH PARAMETERS----
The main DH groups are:
- Group 1. Generated with a 768-bit prime number.
- Group 2. Generated with a 1,024-bit prime number.
- Group 5. Generated with a 1,536-bit prime number.
- Group 14. Generated with a 2,048-bit prime number.
Presentation
References
[1] Adrian, D., Bhargavan, K., Durumeric, Z., Gaudry, P., Green, M., Halderman, J. A., ... & Zimmermann, P. (2015, October). Imperfect forward secrecy: How Diffie-Hellman fails in practice. In Proceedings of the 22nd ACM SIGSAC Conference on Computer and Communications Security (pp. 5-17).
 [
[