The All-Or-Nothing (AONT) method was created by Ronald L. Rivest and encrypts a plaintext block with a random key to create a pseudomessage. Each block is then hashed and then all the hashes are XORed together with the random key to generate the last block of the pseudomessage. The result cannot be reconstructed unless all the blocks are used. In the following we create the hash blocks and then rebuild them all and match the result with the message. [Paper]
All or Nothing Cipher Method |
Outline
We live in a world of encryption keys, in fact, every time we connect to Google we are generating a new encryption key. Our secure data too is often stored using encryption keys. Unfortunately if someone copies our key, they could read all of our data. Also, if we lose our key we might not be able to decrypt our encrypted data. To overcome these problems, we may move to a world where the security of the data is embedded into the data itself - a keyless world!
The All-Or-Nothing (AONT) method was created by Ronald L. Rivest and encrypts a plaintext block with a random key and initialization vector (IV) to create a pseudo-message, which has blocks. Each block is then hashed and then all the hashes are XORed together with the random key to generate the last block of the pseudo-message. The result cannot be reconstructed unless all the blocks are used.
In this page we create the hash blocks and then rebuild them all and match the result with the message.
Here is a sample run:
Original text:
==========
hello
==========
message blocks:
0 TLNhB6DN2ieM64izUeTBUw==
1 eQJZv/thGMFuykT1KcfKkQ==
2 dj8/LA1YPolR+sB4B4HSkw==
They match!
The output is then a number of message blocks, and where each block is the length of the cipher block size. For AES the block size is 128 bits, and for DES it is 64 bits. In the example above we have 26 Base-64 characters, and each represents six bits, so the length of the message block is 24x6 which gives 128 bits. We use a random encryption key, but once the message blocks are created, there is no need for the encryption key, and we can discard it. In this was we do not need to store the encryption key, so it can't be lost.
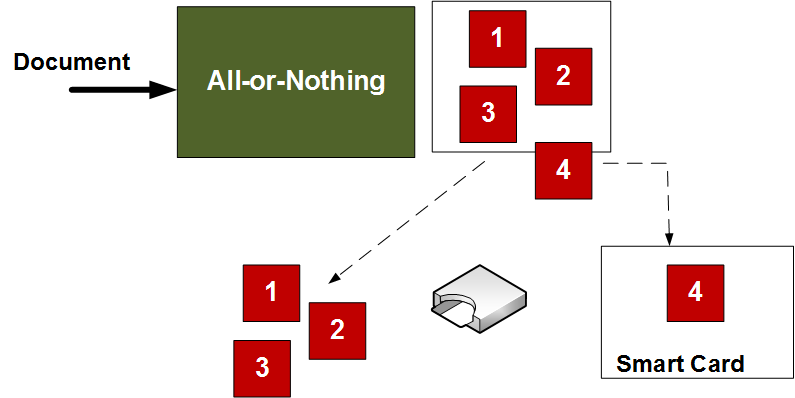
One application of AONT is to take a large file, and break it into the message blocks, and move one part onto a smart card. It will not be possible to rebuild the document unless the smart card provides the last message block. In the following example we create four message blocks, and store three of them on our system, and one on a smart card. Only when we apply the smart card with its message blcok can we rebuild the original document.
Another advantage is that we can use large key sizes, and extremely large documents, and where the message blocks will only be the size of the encryption blocks used in the encryption method. So we could create a network of devices where each kept a single message block, and only when they came together with the other blocks could they recover the original data.
Conclusions
In a world where PKI (Public Key Infrastructure) and the usage of encryption causes many problems, you must wonder if the future of privacy is a world which embeds security into the data and avoid the usage of encryption keys - a keyless system. AONT is one such example.