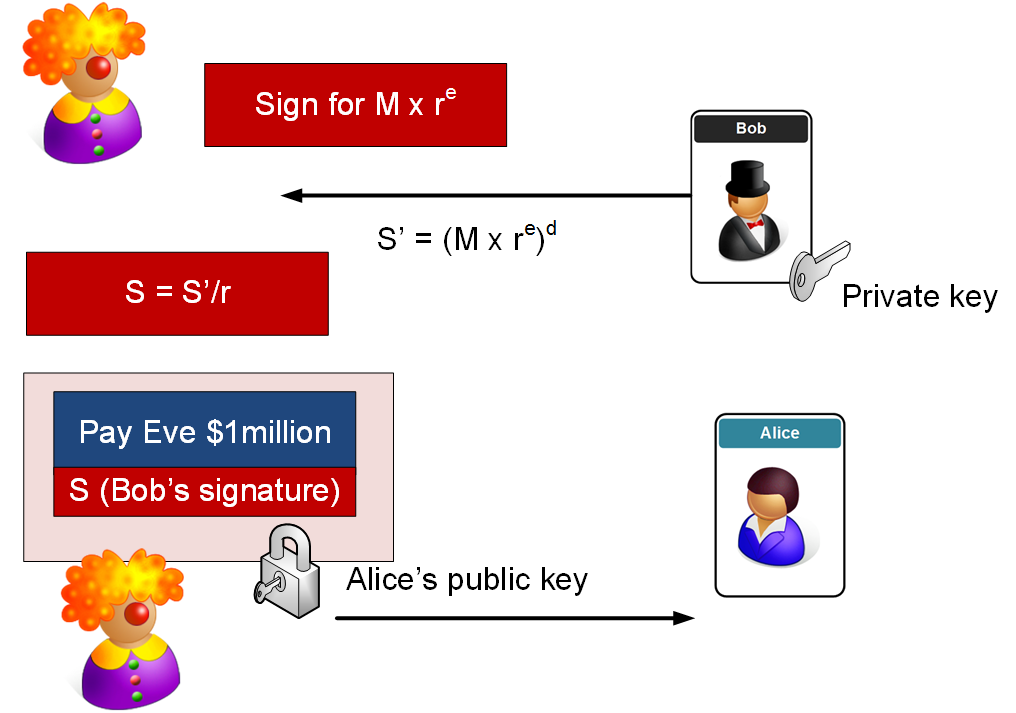
In the blinding attack, we get Bob to sign for a message that is garbled:
Blinding attack |
Outline
Eve has the message (M - "Pay Eve $1 million") and creates another message:
\(M' = r^e M \mod N\)
where e is Bob's encryption key exponent and r is a random number. Eve gets Bob to sign for this. The signature is then:
\(S' = (M')^d \mod N\)
Bob gives S' to Eve, and she just divides by r to get the signature for the original message:
\(\frac{S'}{r} = \frac{(M \times r^e)^d}{r} = \frac{(M^d \times r^{ed})}{r} = \frac{(M^d \times r^{1})}{r} = M^d \mod (N)\)
So Eve takes Bob signature and adds it to the original message that Bob wouldn't sign, and she can prove that Bob signed it. If she is sending to Alice the Banker, she would take the message:
"Pay Eve $1 million"
and add Bob signature for the message (\(\frac{S'}{r}\)), and then encrypt everything with Alice the Banker's public key. Alice will get the encrypted message and decrypts with her private key, and reads the message:
"Pay Eve $1 million"
and she then looks at the signature, and gets Bob's public key and checks the signature. It will match, so she will pays Eve one million dollars from Bob's account. So here are the basic steps:
Coding
In this case we take the salted MD5 hash of the message and then take mod N of it. An outline of the code is:
import sys
import os
import hashlib
import libnum
e=79
d=1019
N=3337
r=21
Message='Pay Eve $1 million'
print('==Initial values ====')
print('e=',e,'d=',d,'N=',N)
print('message=',Message,'r=',r)
print('\n=============')
array = os.urandom(1 << 20)
md5 = hashlib.md5()
md5.update(array)
digest = md5.hexdigest()
M = int(digest, 16) % N
print('MD5 hash (mod N): ',M)
signed=pow(M,d , N)
print('Signed:\t',signed)
val_sent_by_eve = (M*pow(r,e, N))%N
signed_dash = pow(val_sent_by_eve , d , N)
print('Bob sends Eve signature: ',signed_dash)
result= (signed_dash * libnum.invmod(r,N) ) % N
print('Eve send signature of:',result)
print('\n=== Check ==')
unsigned = pow(result,e , N)
print('Unsigned value is:',unsigned)
if (unsigned==M):
print('Success. Bob has signed it')
else:
print('Signatures do not compute')
Key calculation
Let’s select:
P=47 Q=71
The calculation of n and PHI is:
n=P × Q = 13 × 11 = 3337 PHI = (p-1)(q-1) = 3220
We can select e as:
e = 79
Next we can calculate d from:
(79 × d) mod 3220 = 1 [Link] d = 1019 Encryption key [3337,79] Decryption key [3337,1019]
Then, with a message of 688, we get:
\(Cipher = (688)^{79} \mod 3337 = 1570\)
\(Decoded = (1570)^{1019} \mod 3337 = 688\)