If you break SHA-3 away from its fixed length output you get an EXtendable Output Function (XOF). This now has the potential of producing an almost infinite sets of outputs, and where we could thus take a single byte and produce an output of a billion bytes, or even take a billion bytes of input and produce a single byte output. In essence, it is a state generator, and where with given inputs we can reach a well-defined state. We can expose the state to anyone, as they will not know the secrets that allow us to take us to the previous and the next state. This page outlines the SHAKE method [article]:
SHAKE |
Test vectors
The following is a test run for eight bytes
Input word: hello123 Length (bytes): 8 -----SHAKE----- Shake 128 bit: 1b85861510bc4d8e Shake 256 bit: ade612ba265f92de
Code
The following is an outline of the code:
import sys
import hashlib
data="hello"
size=16
if (len(sys.argv)>1):
data=sys.argv[1]
if (len(sys.argv)>2):
size=int(sys.argv[2])
print ('Input word:',data)
print ('Length (bytes):',size)
print ('\n-----SHAKE-----\n')
s = hashlib.shake_128()
s.update(data.encode())
print ('Shake 128 bit: ',s.hexdigest(size))
s = hashlib.shake_256()
s.update(data.encode())
print ('Shake 256 bit: ',s.hexdigest(size))
SHA-3 was known as Keccak and is a hash function designed by Guido Bertoni, Joan Daemen, Michaël Peeters, and Gilles Van Assche. MD5 and SHA-0 have been shown to be susceptible to attacks, along with theoretical attacks on SHA-1. NIST thus defined there was a need for a new hashing method which did not use the existing methods for hashing, and setup a competition for competing algorithms.
In October 2012, Keccak won the NIST hash function competition, and is proposed as the SHA-3 standard. It should be noted that it is not replacement SHA-2, which is currently a secure methods. Overall Keccak uses the sponge construction where the message blocks are XORed into the initial bits of the state, and then invertibly permuted.
The sponge function takes a simple function f and involves a number of stages, and where we create a fixed output (dependent on the bit length of the hash function). Simple operations of XOR, AND, and bit shifts are used, and which leads to a fast generation of the hash function:
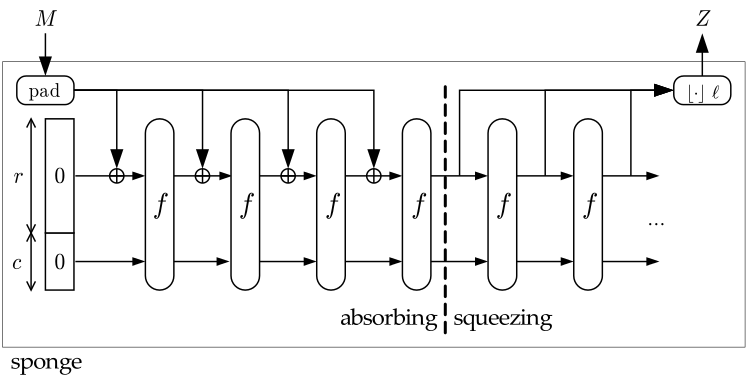
The f permutation function takes a variable-length input and produces an arbitrary output length. A value r is the bit rate, and each f function operates on b bits, and where a capacity is defined as c = b - r.
National Institute of Standards and Technology (NIST) has now released the final version of the method as a new standard: Federal Information Processing Standard (FIPS) 202, SHA-3 Standard: Permutation-Based Hash and Extendable-Output Functions.
NIST published the new standard on 5 August 2015 [here] and which beat off competition from BLAKE (Aumasson et al.), Grøstl (Knudsen et al), JH (Hongjun Wu), and Skein (Schneier et al.).
The SHAKE method is useful as it can be used to create a hash method of a variable length. For example the 128-bit version will produce a hash value is 32 hex characters.
The following is a presentation on SHA-3, SHAKE and Keccak [slides]: