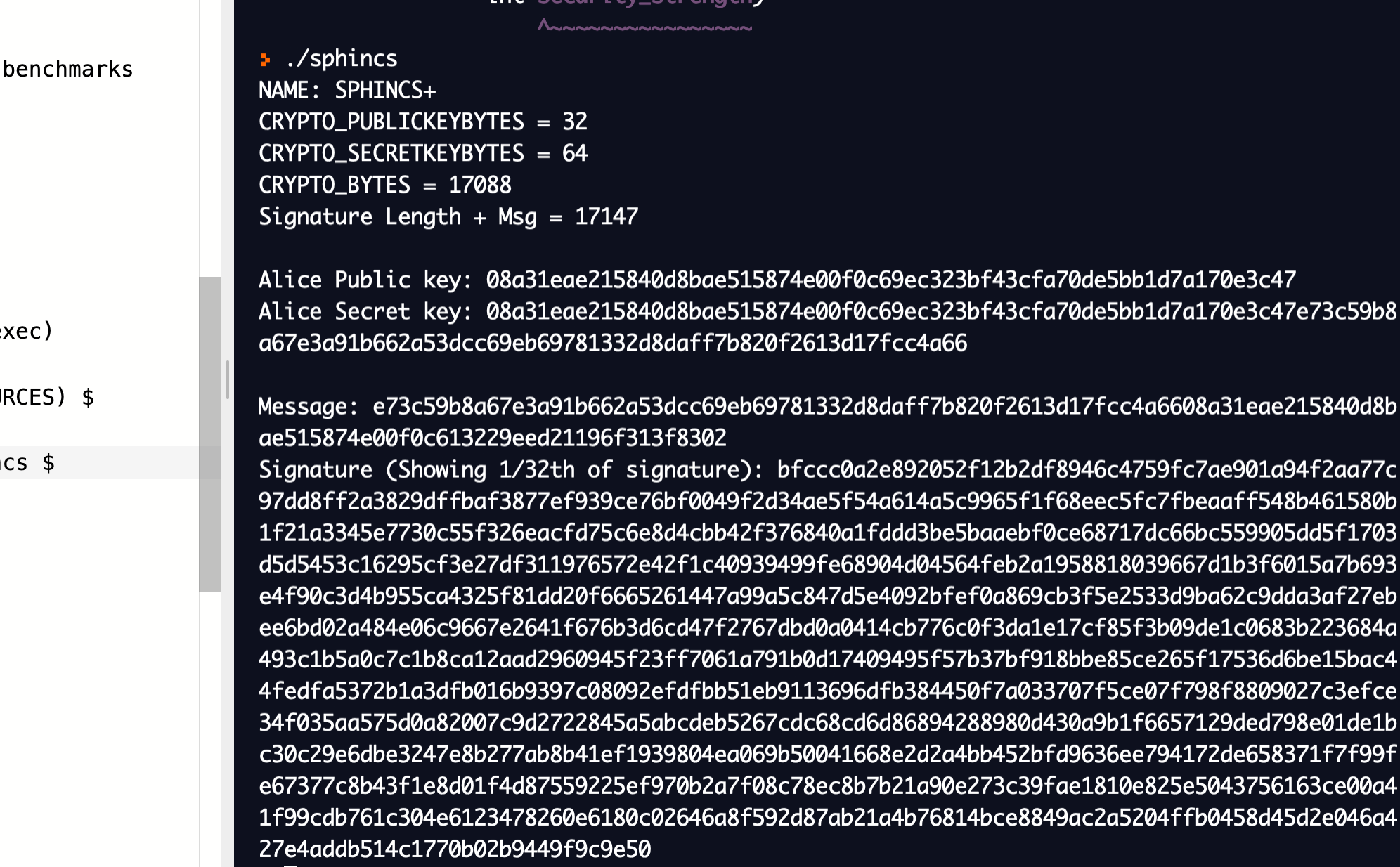
SPHINCS is a stateless hash-based signature scheme, which is quantum robust. It was proposed by Bernstein et al. in 2015 [paper]. SPHINCS+ 256 has a public key size of 1kB, a private key size of 1kB, and a signature of 41 kB. It has been shown to operate at speeds of hundreds of hashes per second on a 4-core 3.5GHz processor.
SPHINCS |
Details
It uses WOTS and HORST for hash-based trees. The code uses a number of parameters:
- n -- length of hash in WOTS / HORST (in bits)
- m -- length of message hash (in bits)
- h -- height of the hyper-tree
- d -- layers of the hyper-tree
- w -- Winternitz parameter used for WOTS signature
- tau -- layers in the HORST tree (2^tau is no. of secret-key elements)
- k -- number of revealed secret-key elements per HORST signature
In the example we use: n=256, m=512, h=2, d=1, w=4, tau=8, k=64.
The hashing method used of some of the operations is BLAKE, and Cha-cha is used to generate a random number.
Coding
The following is an outline (based on code [here]):
import sphincs as SPHINCS
import binascii
# sphincs = SPHINCS(n=256, m=512, h=8, d=2, w=4, tau=8, k=64)
sphincs = SPHINCS.SPHINCS(n=256, m=512, h=2, d=1, w=4, tau=8, k=64)
string = "This is a message"
M = bytes(string, 'utf-8')
sk, pk = sphincs.keygen()
print ("\nSecret key (first element:",binascii.hexlify(sk[0]))
print ("\nPublic key (first element:",binascii.hexlify(pk[0]))
sig = sphincs.sign(M, sk)
s = list(sig)
print ("\nShowing first two elements of signature:")
print (s[0],binascii.hexlify(s[1]))
print ("\nShowing a few addresses:")
print ("Level:1, Subtree=42, left=13",binascii.hexlify(sphincs.address(level=1, subtree=42, leaf=13)))
print ("Level:3, Subtree=231, left=7",binascii.hexlify(sphincs.address(level=3, subtree=231, leaf=7)))
print ("Level:15, Subtree=21, left=2",binascii.hexlify(sphincs.address(level=15, subtree=21, leaf=2)))
print ("Signature verified",sphincs.verify(M, sig, pk))
Reference
[1] Bernstein, D. J., Hülsing, A., Kölbl, S., Niederhagen, R., Rijneveld, J., & Schwabe, P. (2019, November). The SPHINCS+ signature framework. In Proceedings of the 2019 ACM SIGSAC Conference on Computer and Communications Security (pp. 2129-2146) [paper].