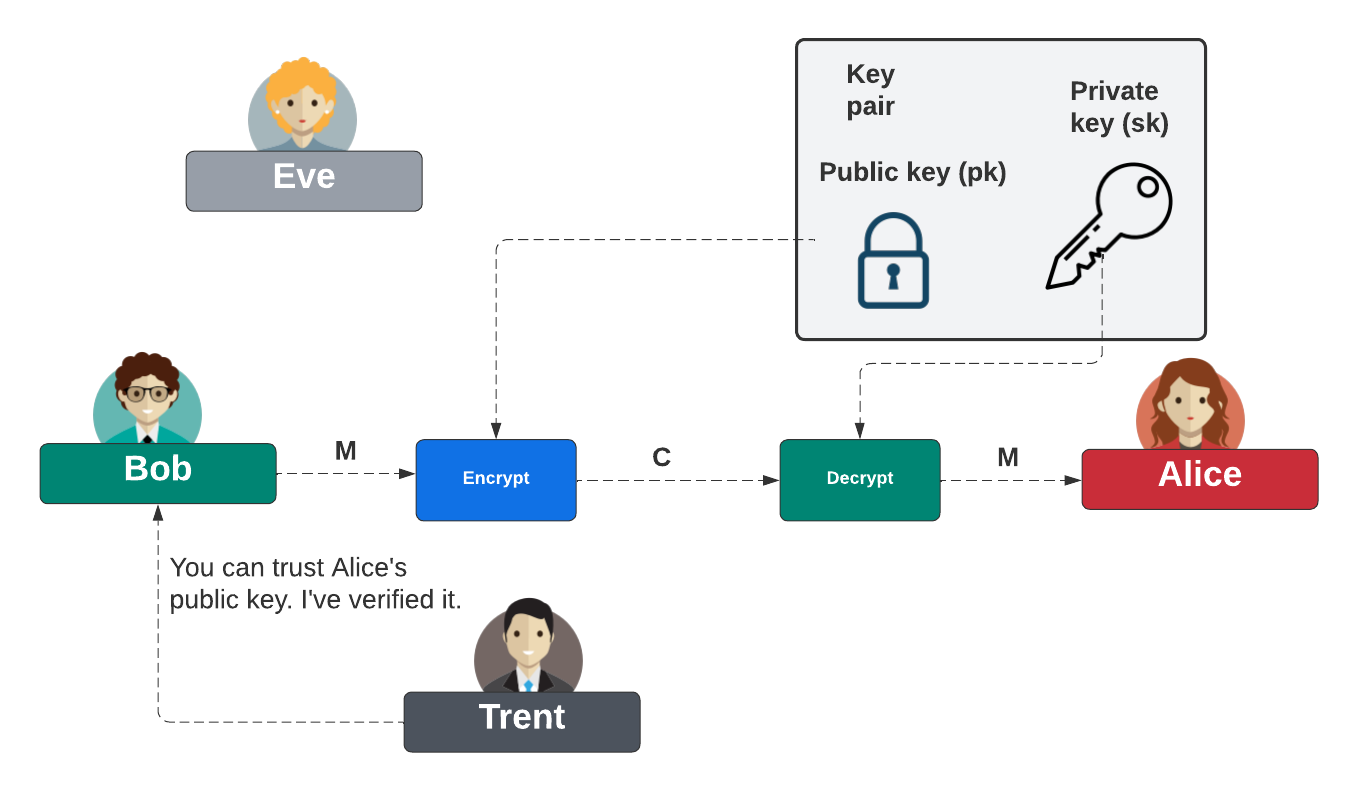
Creating self-signed RSA digital certificates with OpenSSLA digital certificate is defined in the form of X509, and normally contains a trusted public key. For this we sign the certificate with the private key of a trusted entity. But we can also create a self signed certificate, and where we sign with our own private key. The two main formats for a digital certificate is with PEM or DER (a binary form). In this case we will create an RSA key pair, and then create a self-signed certificate which contains the public key, but which is used with the private key. OutlineBasically, digital certificates are used to hold either the public key or the public key pair — in a trusted way. In the following, Alice sends Bob her public key, and which is signed by Trent. If Bob trusts Trent, then he trusts the public key. Bob can then encrypt data for Alice, and where she then decrypts with her private key:
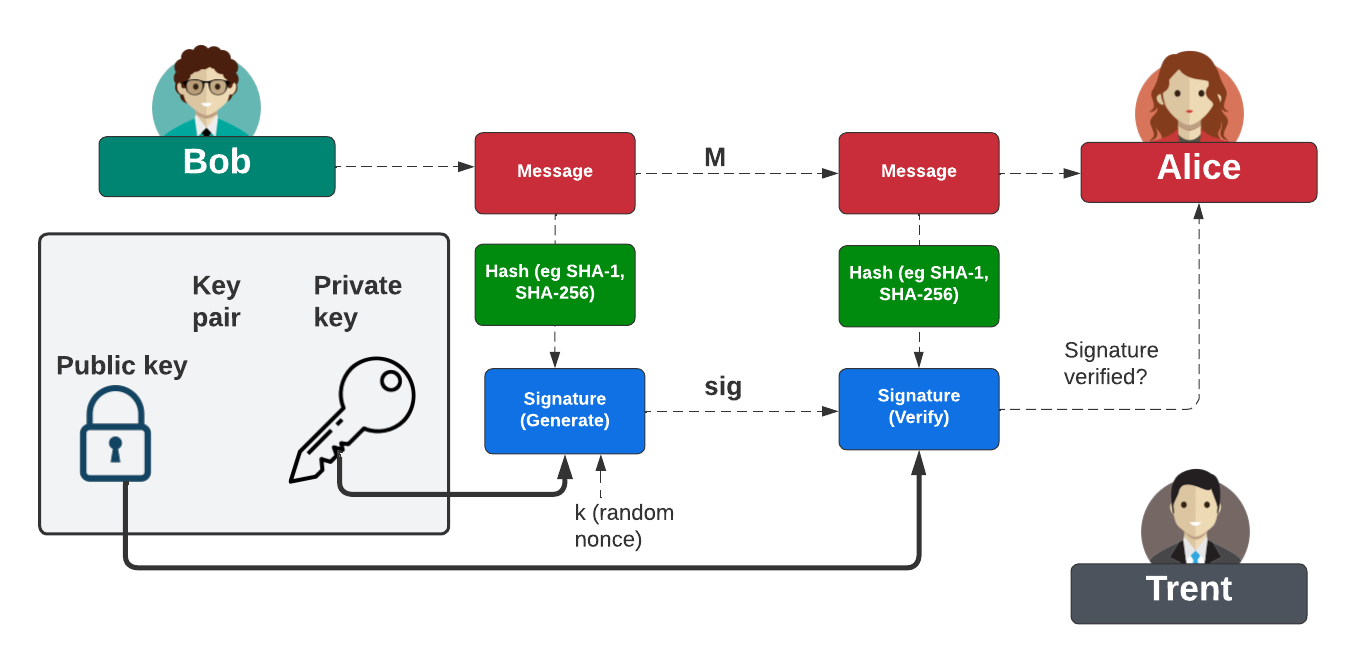
Where we normally use public key encryption is with digital signatures, and where Bob signs a hash of a message with his private key, and then Alice proves his signature with his public key. Again, it is Trent who proves Bob’s public key:
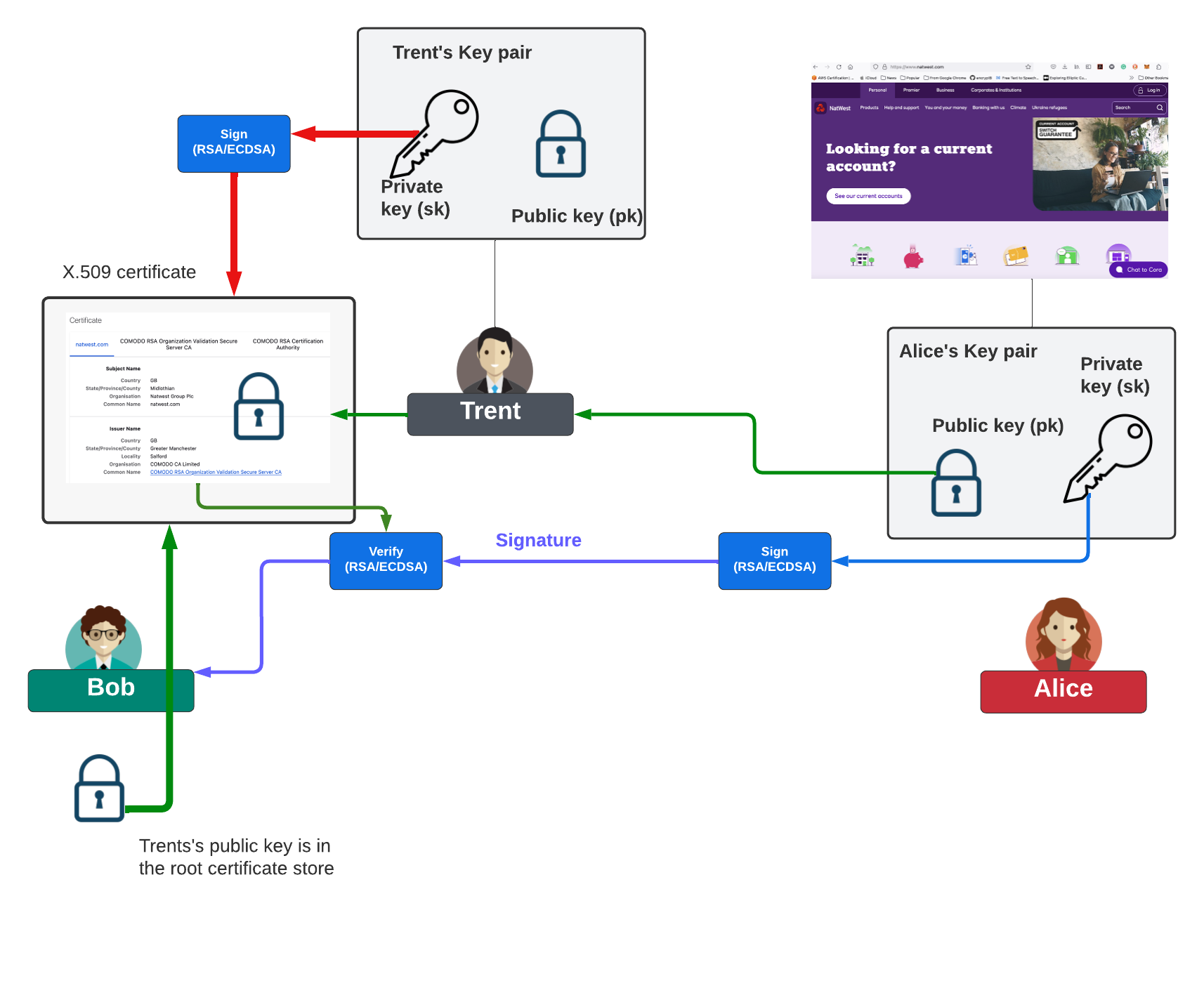
And, where we integrate digital signing to prove the identity of a Web site (Alice) with a digital signature, and where Trent’s private key signs a digital certificate for Alice:
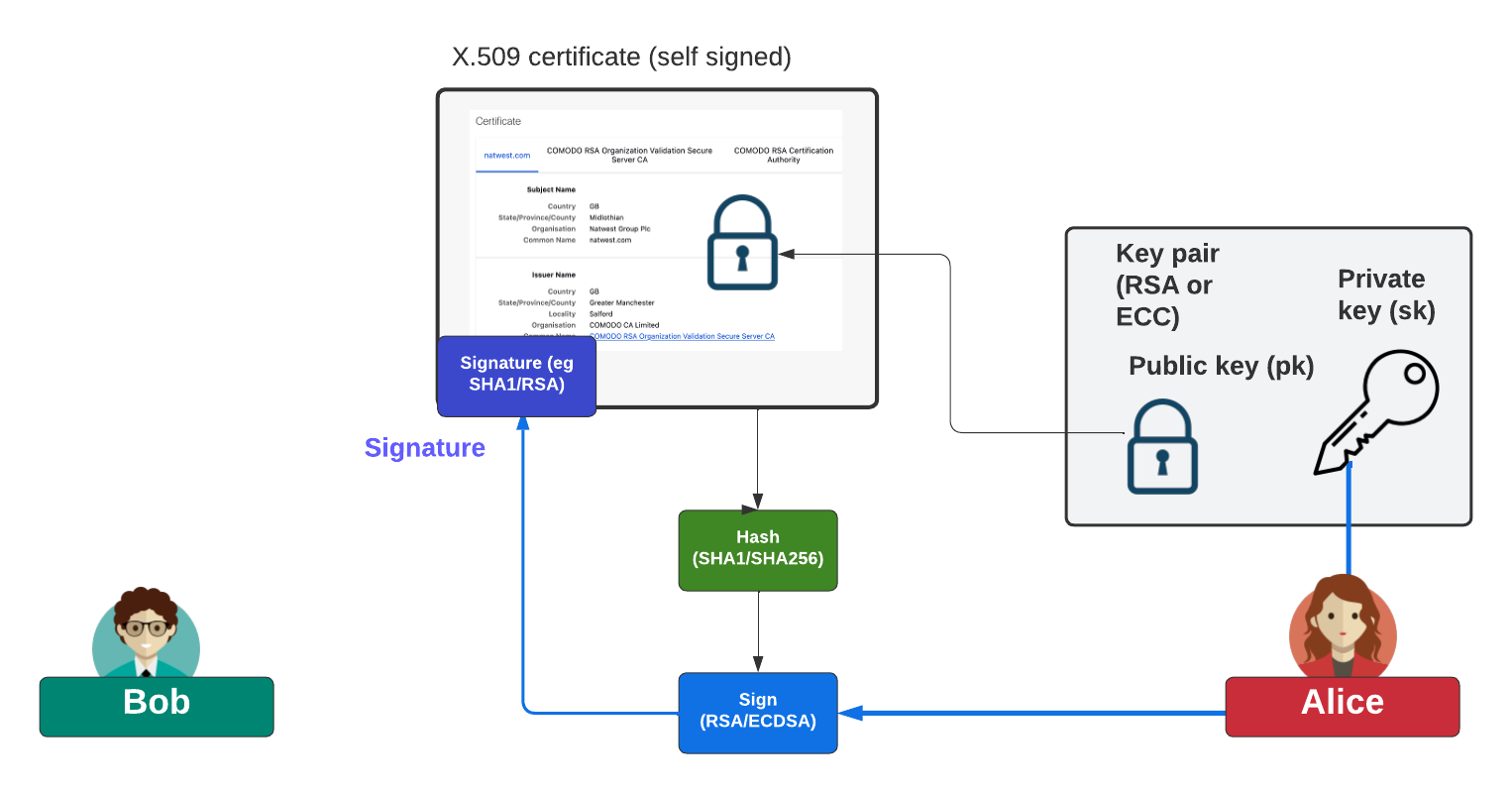
And, so when Bob connects to Alice’s Web site, she signs data with her private key, and then takes her public key from the digital certificate that has been signed by Trent. Overall, Bob will trust this certificate, as he will have Trent’s public key stored on his trusted certificate store. And, so, all digital certificates contain are either the public key of an entity (and which can be distributed publicly), or the key pair (and which should not be distributed publicly). Overall, the two main key pairs we can have, is with RSA keys or ECC (Elliptic Curve Cryptography) key pairs. In this case, we will create a self signed digital certificate, and where Alice creates a key pair, and then puts her public key in the certificate, and then signs it with her private key:
The certificate cannot be properly trusted, though, as Trent has not signed it. This self-signed certificate, though, can be used for testing purposes. DetailsA sample run is: Commands: openssl rsa -in file.key -out file1.der -outform DER openssl x509 -in file.crt -out file2.der -outform DER type file1.der | xxd -pr type file2.der | xxd -pr -----BEGIN PRIVATE KEY----- MIIBVAIBADANBgkqhkiG9w0BAQEFAASCAT4wggE6AgEAAkEA19ishIHxKjHZkeF7 6mLfJ1K6GkFGewc5Z41yFtgOxmEqkKMTT6/JlkwmS5W+RAecdgNRqJ8CBEOvYfQj Q+P/EQIDAQABAkEAiR8rKdrq/GVC1LwsXpCFN5QEil1hixLh0vk2u3Byom85SGYF kaYrbVmRFwFd31Gd3eYXsz7W8m61K2XL/Ba26QIhAO7NhA+PqP+zP+CPshGsGlkZ iyTlFwA2Pi0pPU4W0mirAiEA52PxEiPvJVwWZyfJOpcRsZmpqbyK+12DNI+wgNPF bzMCICEV6E4foVKMCzWZsxovthbSKy0ZcG5fFY48QHopP02xAiAbjpZ+P5NSkrYE UQOxG5661P8UvOScbRWcI+S0YwQnawIgc1BXRn5td4G5HBXMVaCUlLzxpR1ww5fe H1OcsmMXQ5M= -----END PRIVATE KEY----- DER Format (Keys): 3082013a020100024100d7d8ac8481f12a31d991e17bea62df2752ba1a41 467b0739678d7216d80ec6612a90a3134fafc9964c264b95be44079c7603 51a89f020443af61f42343e3ff110203010001024100891f2b29daeafc65 42d4bc2c5e90853794048a5d618b12e1d2f936bb7072a26f3948660591a6 2b6d599117015ddf519ddde617b33ed6f26eb52b65cbfc16b6e9022100ee cd840f8fa8ffb33fe08fb211ac1a59198b24e51700363e2d293d4e16d268 ab022100e763f11223ef255c166727c93a9711b199a9a9bc8afb5d83348f b080d3c56f3302202115e84e1fa1528c0b3599b31a2fb616d22b2d19706e 5f158e3c407a293f4db102201b8e967e3f935292b6045103b11b9ebad4ff 14bce49c6d159c23e4b46304276b0220735057467e6d7781b91c15cc55a0 9494bcf1a51d70c397de1f539cb263174393 -----BEGIN CERTIFICATE----- MIIBoDCCAUqgAwIBAgIUC7BJE9DZUq8iBtxcXs73hBpzsbEwDQYJKoZIhvcNAQEL BQAwFjEUMBIGA1UEAwwLZXhhbXBsZS5jb20wHhcNMjMxMjE3MjAzNTA5WhcNMzMx MjE0MjAzNTA5WjAWMRQwEgYDVQQDDAtleGFtcGxlLmNvbTBcMA0GCSqGSIb3DQEB AQUAA0sAMEgCQQDX2KyEgfEqMdmR4XvqYt8nUroaQUZ7BzlnjXIW2A7GYSqQoxNP r8mWTCZLlb5EB5x2A1GonwIEQ69h9CND4/8RAgMBAAGjcDBuMB0GA1UdDgQWBBTB dEJLuzv10VQgbpuxrago98Ba1jAfBgNVHSMEGDAWgBTBdEJLuzv10VQgbpuxrago 98Ba1jAPBgNVHRMBAf8EBTADAQH/MBsGA1UdEQQUMBKCC2V4YW1wbGUuY29tggMq LjQwDQYJKoZIhvcNAQELBQADQQAxAVB/2XWC5XHatXMLpFO19qyJRdciC3Vl7B9O XVty3/8cM7zGU64GFAI+t4LDTGC0vIYwpeQhvoDF81ziSSBG -----END CERTIFICATE----- DER Format (Certicate): 308201a03082014aa00302010202140bb04913d0d952af2206dc5c5ecef7 841a73b1b1300d06092a864886f70d01010b050030163114301206035504 030c0b6578616d706c652e636f6d301e170d323331323137323033353039 5a170d3333313231343230333530395a30163114301206035504030c0b65 78616d706c652e636f6d305c300d06092a864886f70d0101010500034b00 3048024100d7d8ac8481f12a31d991e17bea62df2752ba1a41467b073967 8d7216d80ec6612a90a3134fafc9964c264b95be44079c760351a89f0204 43af61f42343e3ff110203010001a370306e301d0603551d0e04160414c1 74424bbb3bf5d154206e9bb1ada828f7c05ad6301f0603551d2304183016 8014c174424bbb3bf5d154206e9bb1ada828f7c05ad6300f0603551d1301 01ff040530030101ff301b0603551d1104143012820b6578616d706c652e 636f6d82032a2e34300d06092a864886f70d01010b05000341003101507f d97582e571dab5730ba453b5f6ac8945d7220b7565ec1f4e5d5b72dfff1c 33bcc653ae0614023eb782c34c60b4bc8630a5e421be80c5f35ce2492046 For the keys, we have: 3082013a020100024100d7d8ac8481f12a31d991e17bea62df2752ba1a41 467b0739678d7216d80ec6612a90a3134fafc9964c264b95be44079c7603 51a89f020443af61f42343e3ff110203010001024100891f2b29daeafc65 42d4bc2c5e90853794048a5d618b12e1d2f936bb7072a26f3948660591a6 2b6d599117015ddf519ddde617b33ed6f26eb52b65cbfc16b6e9022100ee cd840f8fa8ffb33fe08fb211ac1a59198b24e51700363e2d293d4e16d268 ab022100e763f11223ef255c166727c93a9711b199a9a9bc8afb5d83348f b080d3c56f3302202115e84e1fa1528c0b3599b31a2fb616d22b2d19706e 5f158e3c407a293f4db102201b8e967e3f935292b6045103b11b9ebad4ff 14bce49c6d159c23e4b46304276b0220735057467e6d7781b91c15cc55a0 9494bcf1a51d70c397de1f539cb263174393 We can parse with [here]:
echo 3082013a020100024100d7d8ac8481f12a31d991e17bea62df2752ba1a41467b0739678d7216d80ec6612a90a3134fafc9964c264b95be44079c760351a89f020443af61f42343e3ff110203010001024100891f2b29daeafc6542d4bc2c5e90853794048a5d618b12e1d2f936bb7072a26f3948660591a62b6d599117015ddf519ddde617b33ed6f26eb52b65cbfc16b6e9022100eecd840f8fa8ffb33fe08fb211ac1a59198b24e51700363e2d293d4e16d268ab022100e763f11223ef255c166727c93a9711b199a9a9bc8afb5d83348fb080d3c56f3302202115e84e1fa1528c0b3599b31a2fb616d22b2d19706e5f158e3c407a293f4db102201b8e967e3f935292b6045103b11b9ebad4ff14bce49c6d159c23e4b46304276b0220735057467e6d7781b91c15cc55a09494bcf1a51d70c397de1f539cb263174393 | xxd -r -p | openssl asn1parse -inform der
0:d=0 hl=4 l= 314 cons: SEQUENCE
4:d=1 hl=2 l= 1 prim: INTEGER :00
7:d=1 hl=2 l= 65 prim: INTEGER :D7D8AC8481F12A31D991E17BEA62DF2752BA1A41467B0739678D7216D80EC6612A90A3134FAFC9964C264B95BE44079C760351A89F020443AF61F42343E3FF11
74:d=1 hl=2 l= 3 prim: INTEGER :010001
79:d=1 hl=2 l= 65 prim: INTEGER :891F2B29DAEAFC6542D4BC2C5E90853794048A5D618B12E1D2F936BB7072A26F3948660591A62B6D599117015DDF519DDDE617B33ED6F26EB52B65CBFC16B6E9
146:d=1 hl=2 l= 33 prim: INTEGER :EECD840F8FA8FFB33FE08FB211AC1A59198B24E51700363E2D293D4E16D268AB
181:d=1 hl=2 l= 33 prim: INTEGER :E763F11223EF255C166727C93A9711B199A9A9BC8AFB5D83348FB080D3C56F33
216:d=1 hl=2 l= 32 prim: INTEGER :2115E84E1FA1528C0B3599B31A2FB616D22B2D19706E5F158E3C407A293F4DB1
250:d=1 hl=2 l= 32 prim: INTEGER :1B8E967E3F935292B6045103B11B9EBAD4FF14BCE49C6D159C23E4B46304276B
284:d=1 hl=2 l= 32 prim: INTEGER :735057467E6D7781B91C15CC55A09494BCF1A51D70C397DE1F539CB263174393
In RSA, a public key is (e,N) and the private key is (d,N), and where N is the modulus and made up of the multiplication of two prime numbers (p and q). In the following, we have hexademical values of e=0x010001, d=0xD7D8AC8481F12A31D991E17BEA62DF2752BA1A41467B0739678D7216D80EC6612A90A3134FAFC9964C264B95BE44079C760351A89F020443AF61F42343E3FF11, N=0x891F2B29DAEAFC6542D4BC2C5E90853794048A5D618B12E1D2F936BB7072A26F3948660591A62B6D599117015DDF519DDDE617B33ED6F26EB52B65CBFC16B6E9, p=0xEECD840F8FA8FFB33FE08FB211AC1A59198B24E51700363E2D293D4E16D268AB and q=0xE763F11223EF255C166727C93A9711B199A9A9BC8AFB5D83348FB080D3C56F33. If we try p times q, we get the modulus value:
>>> p=int("EECD840F8FA8FFB33FE08FB211AC1A59198B24E51700363E2D293D4E16D268AB",16)
>>> q=int("E763F11223EF255C166727C93A9711B199A9A9BC8AFB5D83348FB080D3C56F33",16)
>>> N=hex(p*q)
>>> print (N)
0xd7d8ac8481f12a31d991e17bea62df2752ba1a41467b0739678d7216d80ec6612a90a3134fafc9964c264b95be44079c760351a89f020443af61f42343e3ff11
We can now analyse the certificate, and parse the DER format [here]: This gives:
Command:
echo 308201a03082014aa00302010202140bb04913d0d952af2206dc5c5ecef7841a73b1b1300d06092a864886f70d01010b050030163114301206035504030c0b6578616d706c652e636f6d301e170d3233313231373230333530395a170d3333313231343230333530395a30163114301206035504030c0b6578616d706c652e636f6d305c300d06092a864886f70d0101010500034b003048024100d7d8ac8481f12a31d991e17bea62df2752ba1a41467b0739678d7216d80ec6612a90a3134fafc9964c264b95be44079c760351a89f020443af61f42343e3ff110203010001a370306e301d0603551d0e04160414c174424bbb3bf5d154206e9bb1ada828f7c05ad6301f0603551d23041830168014c174424bbb3bf5d154206e9bb1ada828f7c05ad6300f0603551d130101ff040530030101ff301b0603551d1104143012820b6578616d706c652e636f6d82032a2e34300d06092a864886f70d01010b05000341003101507fd97582e571dab5730ba453b5f6ac8945d7220b7565ec1f4e5d5b72dfff1c33bcc653ae0614023eb782c34c60b4bc8630a5e421be80c5f35ce2492046 | xxd -r -p | openssl asn1parse -inform der
0:d=0 hl=4 l= 416 cons: SEQUENCE
4:d=1 hl=4 l= 330 cons: SEQUENCE
8:d=2 hl=2 l= 3 cons: cont [ 0 ]
10:d=3 hl=2 l= 1 prim: INTEGER :02
13:d=2 hl=2 l= 20 prim: INTEGER :0BB04913D0D952AF2206DC5C5ECEF7841A73B1B1
35:d=2 hl=2 l= 13 cons: SEQUENCE
37:d=3 hl=2 l= 9 prim: OBJECT :sha256WithRSAEncryption
48:d=3 hl=2 l= 0 prim: NULL
50:d=2 hl=2 l= 22 cons: SEQUENCE
52:d=3 hl=2 l= 20 cons: SET
54:d=4 hl=2 l= 18 cons: SEQUENCE
56:d=5 hl=2 l= 3 prim: OBJECT :commonName
61:d=5 hl=2 l= 11 prim: UTF8STRING :example.com
74:d=2 hl=2 l= 30 cons: SEQUENCE
76:d=3 hl=2 l= 13 prim: UTCTIME :231217203509Z
91:d=3 hl=2 l= 13 prim: UTCTIME :331214203509Z
106:d=2 hl=2 l= 22 cons: SEQUENCE
108:d=3 hl=2 l= 20 cons: SET
110:d=4 hl=2 l= 18 cons: SEQUENCE
112:d=5 hl=2 l= 3 prim: OBJECT :commonName
117:d=5 hl=2 l= 11 prim: UTF8STRING :example.com
130:d=2 hl=2 l= 92 cons: SEQUENCE
132:d=3 hl=2 l= 13 cons: SEQUENCE
134:d=4 hl=2 l= 9 prim: OBJECT :rsaEncryption
145:d=4 hl=2 l= 0 prim: NULL
147:d=3 hl=2 l= 75 prim: BIT STRING
0000 - 00 30 48 02 41 00 d7 d8-ac 84 81 f1 2a 31 d9 91 .0H.A.......*1..
0010 - e1 7b ea 62 df 27 52 ba-1a 41 46 7b 07 39 67 8d .{.b.'R..AF{.9g.
0020 - 72 16 d8 0e c6 61 2a 90-a3 13 4f af c9 96 4c 26 r....a*...O...L.
0030 - 4b 95 be 44 07 9c 76 03-51 a8 9f 02 04 43 af 61 K..D..v.Q....C.a
0040 - f4 23 43 e3 ff 11 02 03-01 00 01 .#C........
224:d=2 hl=2 l= 112 cons: cont [ 3 ]
226:d=3 hl=2 l= 110 cons: SEQUENCE
228:d=4 hl=2 l= 29 cons: SEQUENCE
230:d=5 hl=2 l= 3 prim: OBJECT :X509v3 Subject Key Identifier
235:d=5 hl=2 l= 22 prim: OCTET STRING
0000 - 04 14 c1 74 42 4b bb 3b-f5 d1 54 20 6e 9b b1 ad ...tBK.;..T n...
0010 - a8 28 f7 c0 5a d6 .(..Z.
259:d=4 hl=2 l= 31 cons: SEQUENCE
261:d=5 hl=2 l= 3 prim: OBJECT :X509v3 Authority Key Identifier
266:d=5 hl=2 l= 24 prim: OCTET STRING
0000 - 30 16 80 14 c1 74 42 4b-bb 3b f5 d1 54 20 6e 9b 0....tBK.;..T n.
0010 - b1 ad a8 28 f7 c0 5a d6- ...(..Z.
292:d=4 hl=2 l= 15 cons: SEQUENCE
294:d=5 hl=2 l= 3 prim: OBJECT :X509v3 Basic Constraints
299:d=5 hl=2 l= 1 prim: BOOLEAN :255
302:d=5 hl=2 l= 5 prim: OCTET STRING
0000 - 30 03 01 01 ff 0....
309:d=4 hl=2 l= 27 cons: SEQUENCE
311:d=5 hl=2 l= 3 prim: OBJECT :X509v3 Subject Alternative Name
316:d=5 hl=2 l= 20 prim: OCTET STRING
0000 - 30 12 82 0b 65 78 61 6d-70 6c 65 2e 63 6f 6d 82 0...example.com.
0010 - 03 2a 2e 34 .*.4
338:d=1 hl=2 l= 13 cons: SEQUENCE
340:d=2 hl=2 l= 9 prim: OBJECT :sha256WithRSAEncryption
351:d=2 hl=2 l= 0 prim: NULL
353:d=1 hl=2 l= 65 prim: BIT STRING
0000 - 00 31 01 50 7f d9 75 82-e5 71 da b5 73 0b a4 53 .1.P..u..q..s..S
0010 - b5 f6 ac 89 45 d7 22 0b-75 65 ec 1f 4e 5d 5b 72 ....E.".ue..N][r
0020 - df ff 1c 33 bc c6 53 ae-06 14 02 3e b7 82 c3 4c ...3..S........L
0030 - 60 b4 bc 86 30 a5 e4 21-be 80 c5 f3 5c e2 49 20 `...0..!....\.I
0040 - 46
We can see the main certificate elements of sha256WithRSAEncryption (for the signature method), the common name ("example.com"), rsaEncryption (and showing the public key).The key is in a DER format of "30 48 02 41 00 d7 d8 ac 84 81 f1 2a 31 d9 91 e1 7b ea 62 df 27 52 ba 1a 41 46 7b 07 39 67 8d 72 16 d8 0e c6 61 2a 90 a3 13 4f af c9 96 4c 26 4b 95 be 44 07 9c 76 03 51 a8 9f 02 04 43 af 61 f4 23 43 e3 ff 11 02 03 01 00 01". For this we get [here]:
3048024100d7d8ac8481f12a31d991e17bea62df2752ba1a41467b0739678d7216d80ec6612a90a3134fafc9964c264b95be44079c760351a89f020443af61f42343e3ff110203010001 | xxd -r -p | openssl asn1parse -inform der
0:d=0 hl=2 l= 72 cons: SEQUENCE
2:d=1 hl=2 l= 65 prim: INTEGER :D7D8AC8481F12A31D991E17BEA62DF2752BA1A41467B0739678D7216D80EC6612A90A3134FAFC9964C264B95BE44079C760351A89F020443AF61F42343E3FF11
69:d=1 hl=2 l= 3 prim: INTEGER :010001
and where we have the public key of the generated key (N=0xD7D... and E=0x010001). Display cert in textFor the full details of the certificate, we can either specify the PEM or DER file, and display the certificate in a text format:
% openssl x509 -inform pem -noout -text -in cert.crt
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
0b:b0:49:13:d0:d9:52:af:22:06:dc:5c:5e:ce:f7:84:1a:73:b1:b1
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = example.com
Validity
Not Before: Dec 17 20:35:09 2023 GMT
Not After : Dec 14 20:35:09 2033 GMT
Subject: CN = example.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (512 bit)
Modulus:
00:d7:d8:ac:84:81:f1:2a:31:d9:91:e1:7b:ea:62:
df:27:52:ba:1a:41:46:7b:07:39:67:8d:72:16:d8:
0e:c6:61:2a:90:a3:13:4f:af:c9:96:4c:26:4b:95:
be:44:07:9c:76:03:51:a8:9f:02:04:43:af:61:f4:
23:43:e3:ff:11
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Subject Key Identifier:
C1:74:42:4B:BB:3B:F5:D1:54:20:6E:9B:B1:AD:A8:28:F7:C0:5A:D6
X509v3 Authority Key Identifier:
C1:74:42:4B:BB:3B:F5:D1:54:20:6E:9B:B1:AD:A8:28:F7:C0:5A:D6
X509v3 Basic Constraints: critical
CA:TRUE
X509v3 Subject Alternative Name:
DNS:example.com, DNS:*.4
Signature Algorithm: sha256WithRSAEncryption
Signature Value:
31:01:50:7f:d9:75:82:e5:71:da:b5:73:0b:a4:53:b5:f6:ac:
89:45:d7:22:0b:75:65:ec:1f:4e:5d:5b:72:df:ff:1c:33:bc:
c6:53:ae:06:14:02:3e:b7:82:c3:4c:60:b4:bc:86:30:a5:e4:
21:be:80:c5:f3:5c:e2:49:20:4
|
 [
[