HMAC (hash-based message authentication code) supports the usage of a key to hash data. This key is kept secret between Bob and Alice, and can be used to authenticate both the data and that the sender still knows the secret. Overall HMAC can be used with a range of different hashing methods, such as MD5, SHA-1, SHA-256 (SHA-2) and SHA-3. In this case we will use OpenSSL to generate the HMAC value.
HMAC with OpenSSL |
Theory
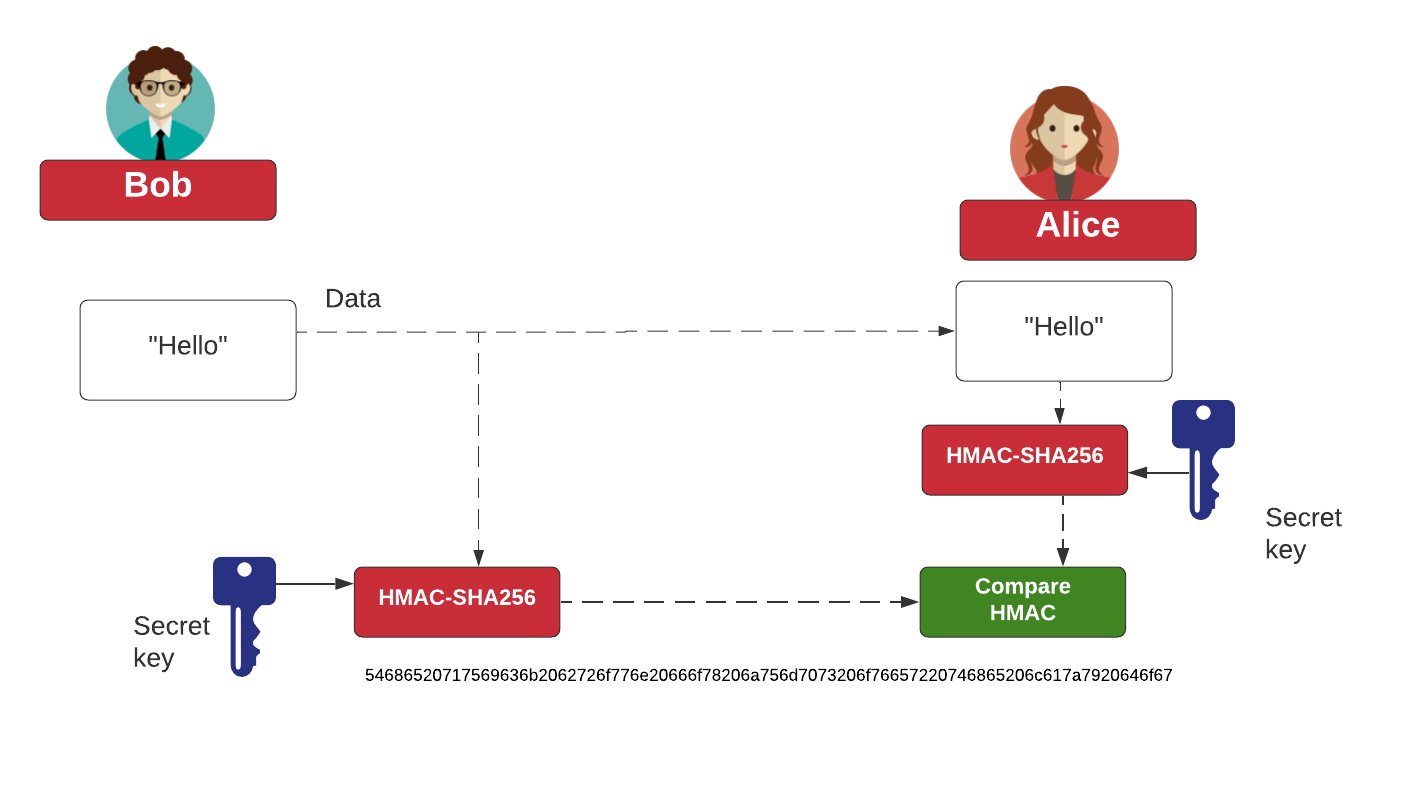
HMAC is a message authentication code (MAC) that can be used to verify the integrity and authentication of a message. It involves hashing the message with a secret key and thus differs from standard hashing, which is purely a one-way function. As with any MAC, it can be used with a standard hash function, such as MD5 or SHA-1, which results in methods such as HMAC-MD5 or HMAC-SHA-1. Also, as with any hashing function, the strength depends on the quality of the hashing function, and the resulting number of hash code bits. Along with this, the number of bits in the secret key is a factor in the strength of the hash. The figure below outlines the operation, where the message to be sent is converted with a secret key, and the hashing function, to an HMAC code. This is then sent with the message. On receipt, the receiver recalculates the HMAC code from the same secret key, and the message, and checks it against the received version. If they match, it validates both the sender and the message.
Outline
The followng is an example of an HMAC with "Hello", and with a key of "test", and a hashing method of SHA-256:
Message: Hello Password: test Hash: sha256 ======================== HMAC: "echo set /p="Hello" | openssl dgst -sha256 -hmac test" e2bb88dfaff4fea88d7dc7a00d18b79bb971653de0fe54c7f3985e4daa1e6a25
and for MD5:
Message: Hello Password: test Hash: md5 ======================== HMAC: Windows command: "echo set /p="Hello" | openssl dgst -md5 -hmac test" Linux command: "echo -n "Hello" | openssl dgst -md5 -hmac test" Result: 5d65fd8cfedbbd814e2650eb25f69c39
 [
[