PGP, GPG and Box
This page outlines some applications of PGP (Pretty Good Privacy), GPG (GNU Privacy Guard) and Box. GPG (Overview)
Key Generation
Key Viewing
Signature Generation and Verification
Encrypting with public key (RSA and ElGamal)
Box Encryption
Symmetric Key encryption with GPG
Age encryption
|
Philip Zimmermann
In June 1991, Philip Zimmermann created the first release of PGP (v1.0):
In a GDPR era, Phil could see the future clearly:
PGP empowers people to take their privacy into their own hands. There has been a growing social need for it. That’s why I wrote it.
Phil Zimmerman was one of the first to face up to defence agencies with his PGP software, which, when published in 1991, allowed users to send encrypted and authenticated emails. For this, the United States Customs Service filed a criminal investigation for a violation in the Arms Export Control Act, and where cryptographic software was seen as a munition. Eventually, the charges were dropped.
Why doesn’t the community push for better standards? Well, could it be that the status quo is a comfortable place to be for many corporations, and where they can snoop on their employee’s emails?
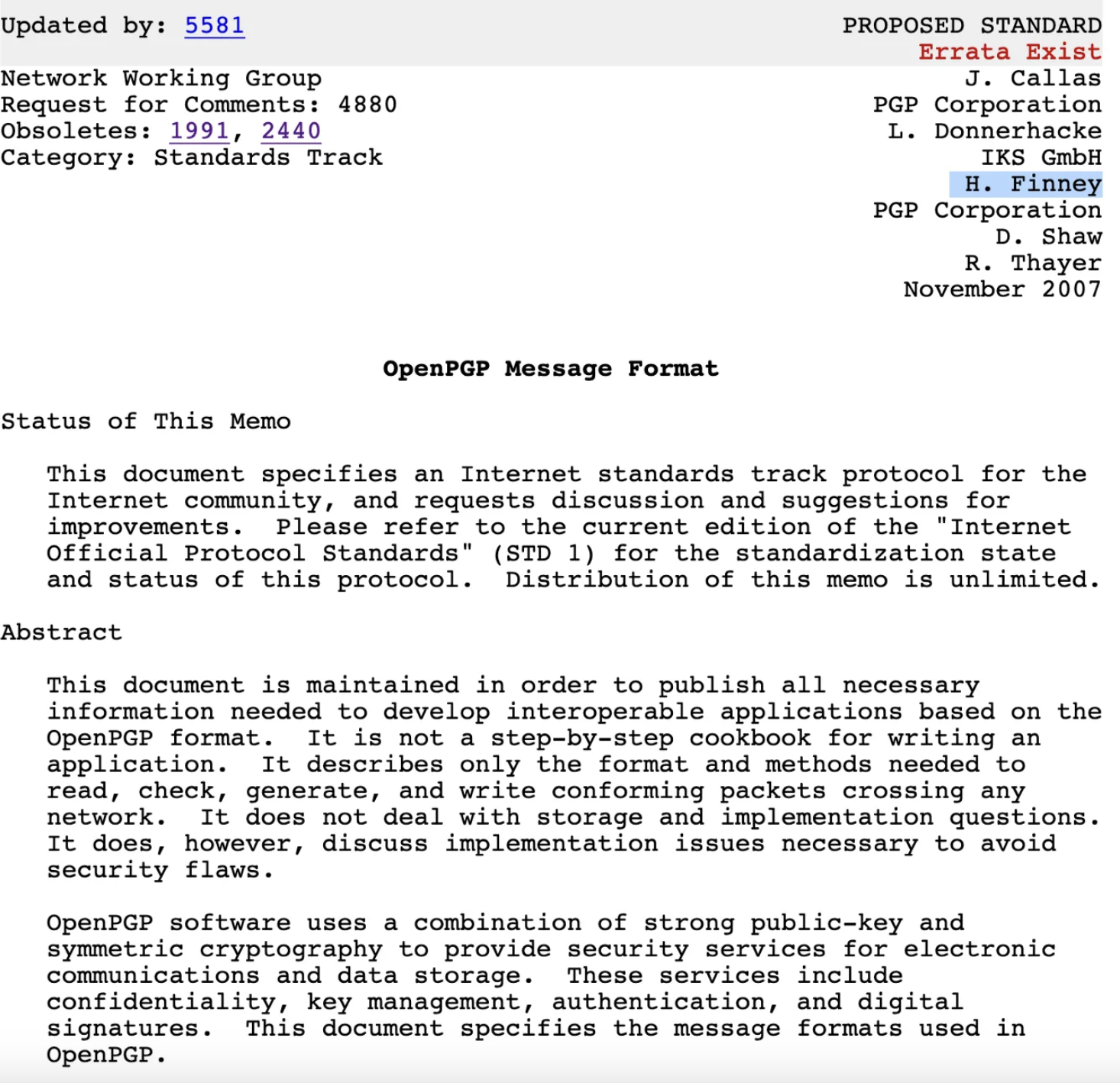
Hal Finney — sadly departed — was also the second developer hired for the PGP Corporation, after Phil Zimmerman, and he is quoted that he loved the technology as it protected the rights of individuals to privacy. He remained there until his retirement in 2011.
Hal was completely enchanted by the magic of cryptography and his Web page announced:
Much of my free time and effort these days are devoted to my activities in cryptography. In the past, I have participated actively on the Cypherpunks mailing list. Cypherpunks Archives seem to go down suspiciously often; too much “burn before reading” stuff there, I guess.
and for PGP:
I was one of the original programmers on PGP version 2.0, working directly with Philip Zimmermann, author of the program. Today, I work for Network Associates, developing the crypto library for the commercial version of PGP.
In 2007 it took a step towards a standard as RFC 4880 — note Hal Finney’s name on the list of authors:
How does PGP work?
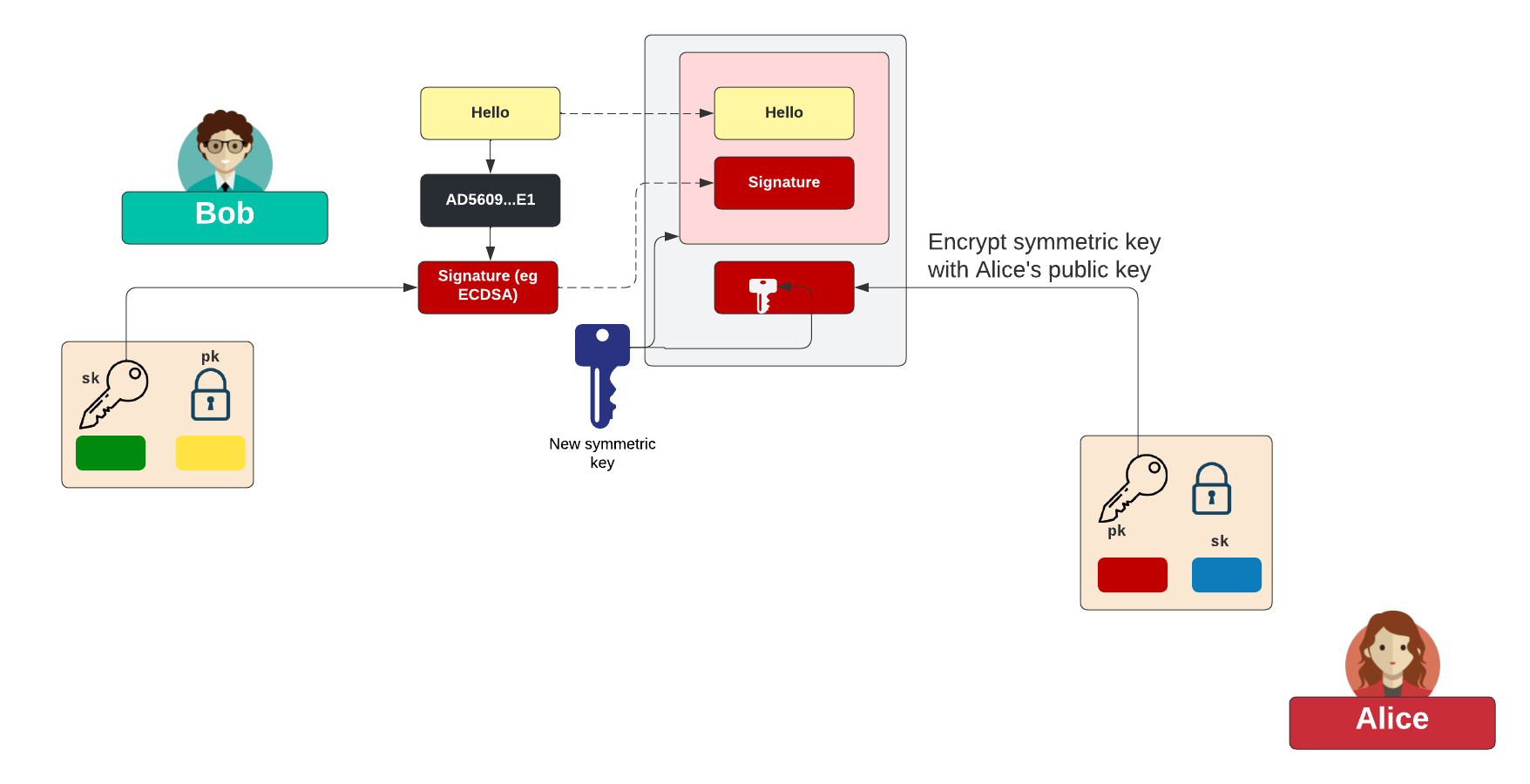
With PGP we do not encrypt the data with public key encryption, for that symmetric keys are much more efficient. For this Bob takes a hash of the message, and then signs this with his private key. Next, he takes the message and the signature and then creates a new symmetric key (K). This is then used to encrypt both the data and the signature. Next, he takes Alice’s public key, and encrypts K. This encrypted key can then be added to the encrypted message:
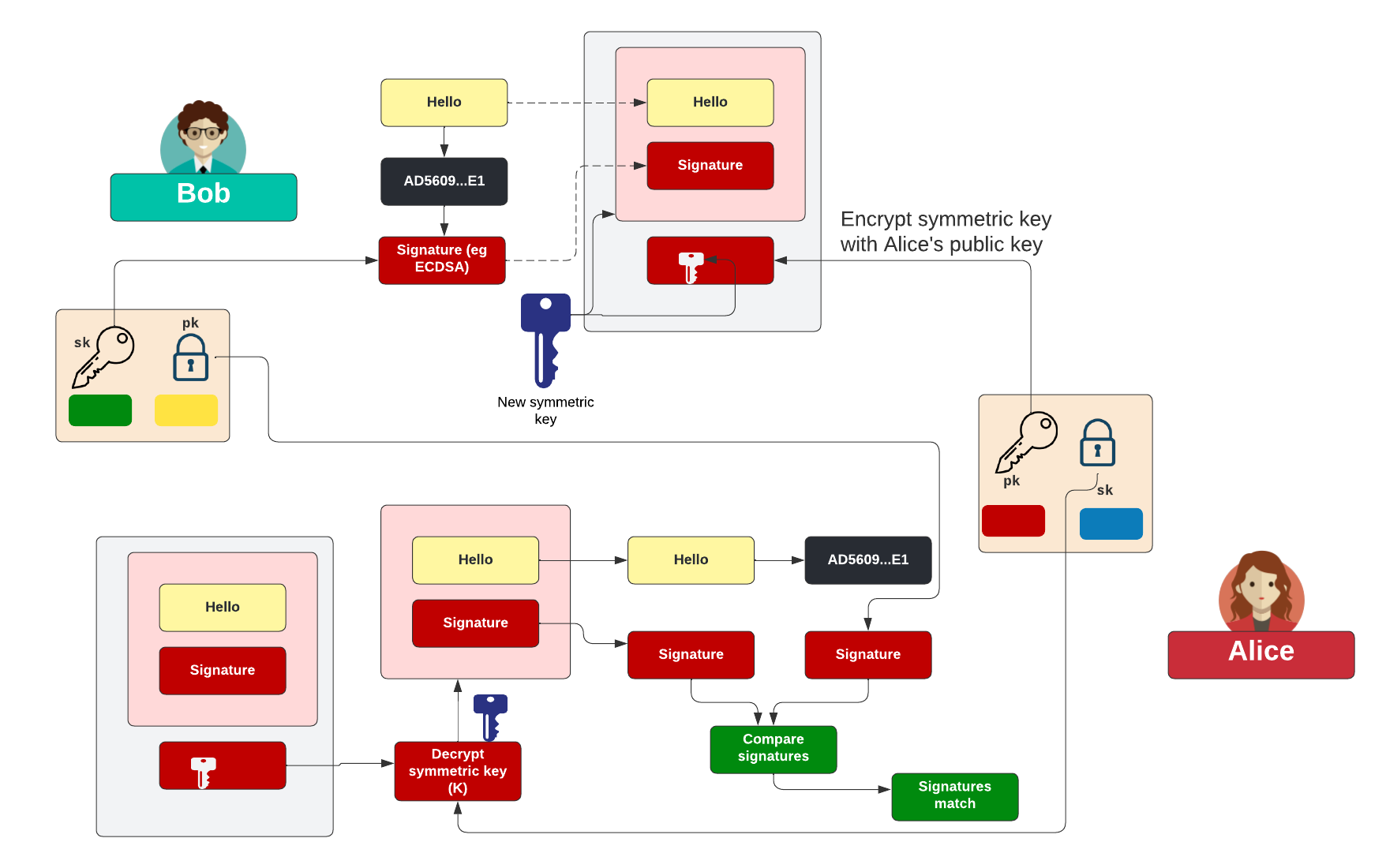
To decrypt, Alice takes the encrypted key and decrypts it with her private key. She can then decrypt the message and reveal the signature. She can now read the message. To check it was Bob who sent the message, she checks the signature of the message with Bob’s public key and if the signature checks out, she knows it was Bob who sent it, and that it has not been changed:
Practical PGP
So let’s send a message of “So did NSA put a backdoor?” and we will apply a password of “qwerty” with 256-bit AES. With PGP we can encode to an armor file format, and which can be easily integrated into an email message:
To generate the key pair we use:
> gpg --keygen
Now export your public key using the form of:
> gpg --export -a "Your name" > mypub.key
We can then view the public key with:
-----BEGIN PGP PUBLIC KEY BLOCK----- mQINBGAtkzYBEACkIejC2VRgZQ9uWwDlgdwtzNb6zQ3TPk6hU604XB+8eYAhM8q7 +u19vbnKQfT+asaunJO6VGdTAyUwJqYAnQAguAMOJpYcMVfLFdFkxmJ/WHssxtZN Y5Y0uJ8w5jQhPhBTN0CIFBgcM95gUxADbIDZoxhL8PcCz7C/d9a1AItZLg/QWkXp .... 2MEBjT9tTsCF+JJdjkEu9+JfEBJScpe254QVIN0BIWpN9Yiboq4PJWgazxtxPjNf cDsx8KpdKAuqi/uq5NPooCTmx2UN3qZC9dX1vBAxSggIt29Xg0EQyW8FW7cL/C2I SN5Ngz5QUKuN0BeOnqRoPaBdFrTTnW7uXsl4LXpP23rfpisKVtEfiXb13322SByX gTAYItr3IsyMEYriggMBpjqKaE3TxdwxETxHh9ktvj5aITWHWkq7corz/hR+POnF nucbcNB98DkLlND905oV =XVeB -----END PGP PUBLIC KEY BLOCK-----
We can then use GPG to generate the cipher message for the email. First, we create the message:
> type 1.txt So did NSA put a backdoor?
Next, we create an amor file with the encrypted message:
> gpg -c -a 1.txt
We can then list the encrypted file:
> type 1.txt.asc -----BEGIN PGP MESSAGE----- Version: GnuPG v2jA0EBwMCz1yj3ME13Nae0lQBp7yb3F1PpsC6J0Qe/3UXsh0P4HIxKzslPdXROGrh VtpKmtVUiLhEFFpHzdgEaFwCLBM/EP86dN7YVJBztoP/trM+Ib5j4buNv+EdGCra X5YPeJc= =BAb2 -----END PGP MESSAGE-----
This is the message that is pasted into the email. Finally, we decrypt with the given password:
> pgp -d 1.txt.asc So did NSA put a backdoor?

 [
[