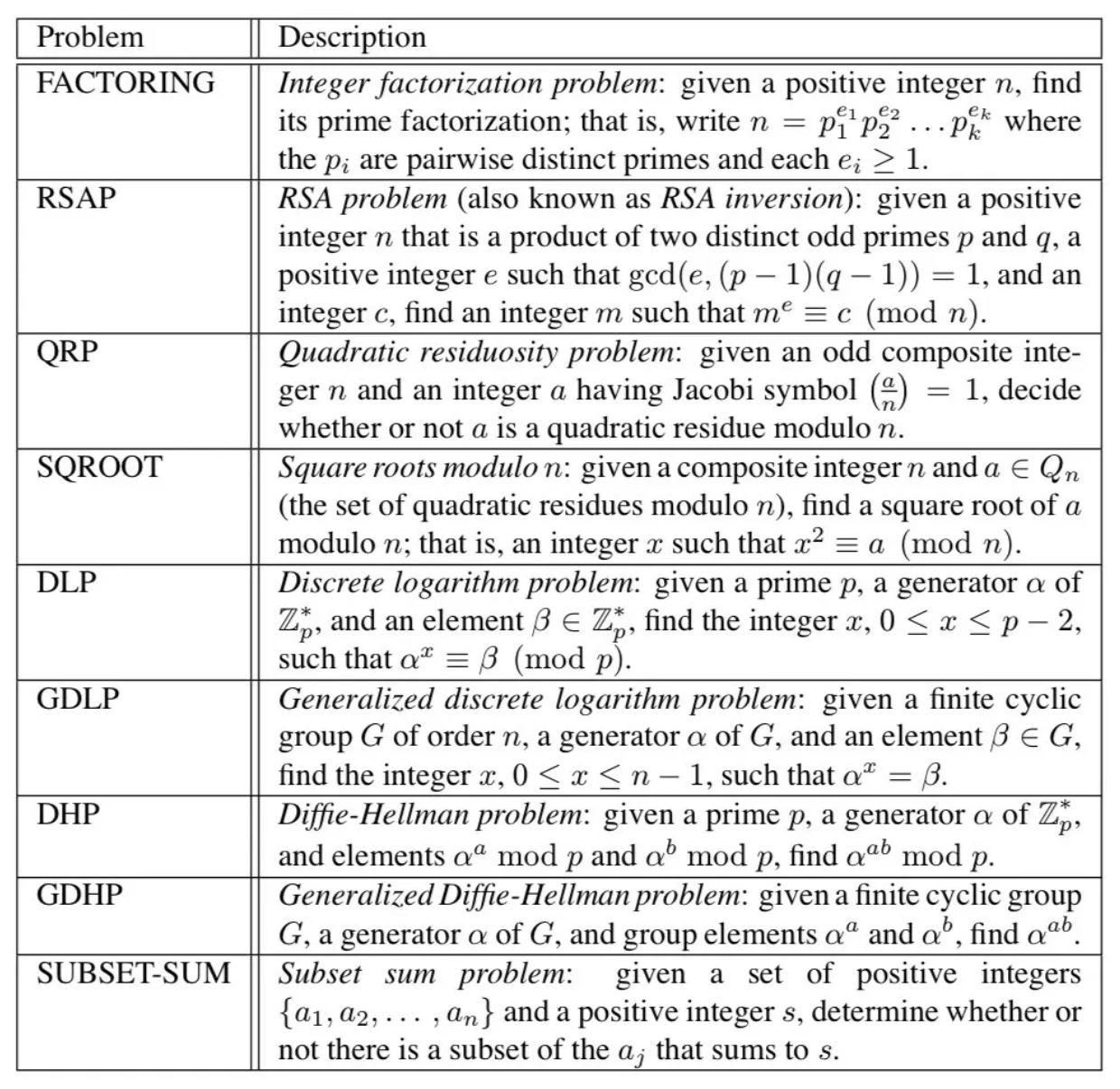
Within public key encryption, one of the intractable problems is related to computing square roots in \( \mathbb{Z}_n\). For this we have \(x^2=a \pmod p\), and where \(a\) is the square root of \(x\) modulo p. If \(p\) is a prime number, the roots are computed using \(p = 5 \pmod 8\). In this case, we will create a prime number which has a given number of bits. This is the quadratic residue.
 [
[