Concise Binary Object Representation (CBOR) [1] integrates security into small data objects and small message sizes. COSE (CBOR Object Signing and Encryption) [2] can then build on this to include signatures, message authentication codes (MACs) and encryption and creating serialised objects. In this case we will use a symmetric key to encrypt a message, and then decrypt it. Bob will take the message and the shared secret key, and create an HMAC message. Alice will then check the HMAC value based on the message received and the shared secret key.
COSE and CBOR - HMAC |
Outline
In computer security, we often have to represent binary data, in single values or groups of characters, bytes, words, long words, signed integers, floating-point values, double-precision floating-point values, and so on. This might be in the form of a data object, a signature or even encrypted content. For this, the ANS.1 DER format is often used, such as presenting digital certificates and signatures. An improvement on this for small messages with security is Concise Binary Object Representation (CBOR) — and which is defined in RFC8949 [1]. While JSON represents text-based data objects CBOR focuses on binary objects. It has been designed to create a lightweight encoder and decoder. This supports the use of CBOR within an IoT infrastructure. The data, also, does not require a data schema to be able to decode it, along with being extensible.
CBOR integrates security into small data objects and small message sizes. This includes signatures, message authentication codes (MACs), encryption and creating serialised objects. In this case we will use a symmetric key to encrypt a message, and then decrypt it. Bob will take the message and the shared secret key, and create an HMAC message. Alice will then check the HMAC value based on the message received and the shared secret key.
from cwt import COSE, COSEKey
from binascii import unhexlify,hexlify
import sys
from os import urandom
mymsg='hello'
method="HS256"
if (len(sys.argv)>1):
mymsg=str(sys.argv[1])
if (len(sys.argv)>2):
method=str(sys.argv[2])
key=urandom(32)
ctx = COSE.new(alg_auto_inclusion=True, kid_auto_inclusion=True)
mac_key = COSEKey.from_symmetric_key(key=key,alg=method, kid="myid")
encoded = ctx.encode_and_mac(mymsg.encode(), mac_key)
print ("Message: ",mymsg)
print ("Key: ",hexlify(key).decode())
#print ("COSE Key: ",mac_key.key)
print ("Method: ",method)
print ("\nMAC code: ",hexlify(encoded))
print ("\nDecoded: ",ctx.decode(encoded, mac_key).decode())
The IV value applied in this case is random 16 byte value (128 bits). A sample run shows the format of the key and message, and where we can encode the encrypted data object into a hex stream:
Message: fdfd Key: a53542e34698d32f89b7e16cc0f5e60c602ff2bb51f594ea08f998b0ae9b8456 Method: HS256 MAC code: b'd18443a10105a104446d7969644466646664582051ab4ac12625bf288d7a04788f638ac36f7173c94542c78e2ade4184e8cc3e3f' Decoded: fdfd
Coding
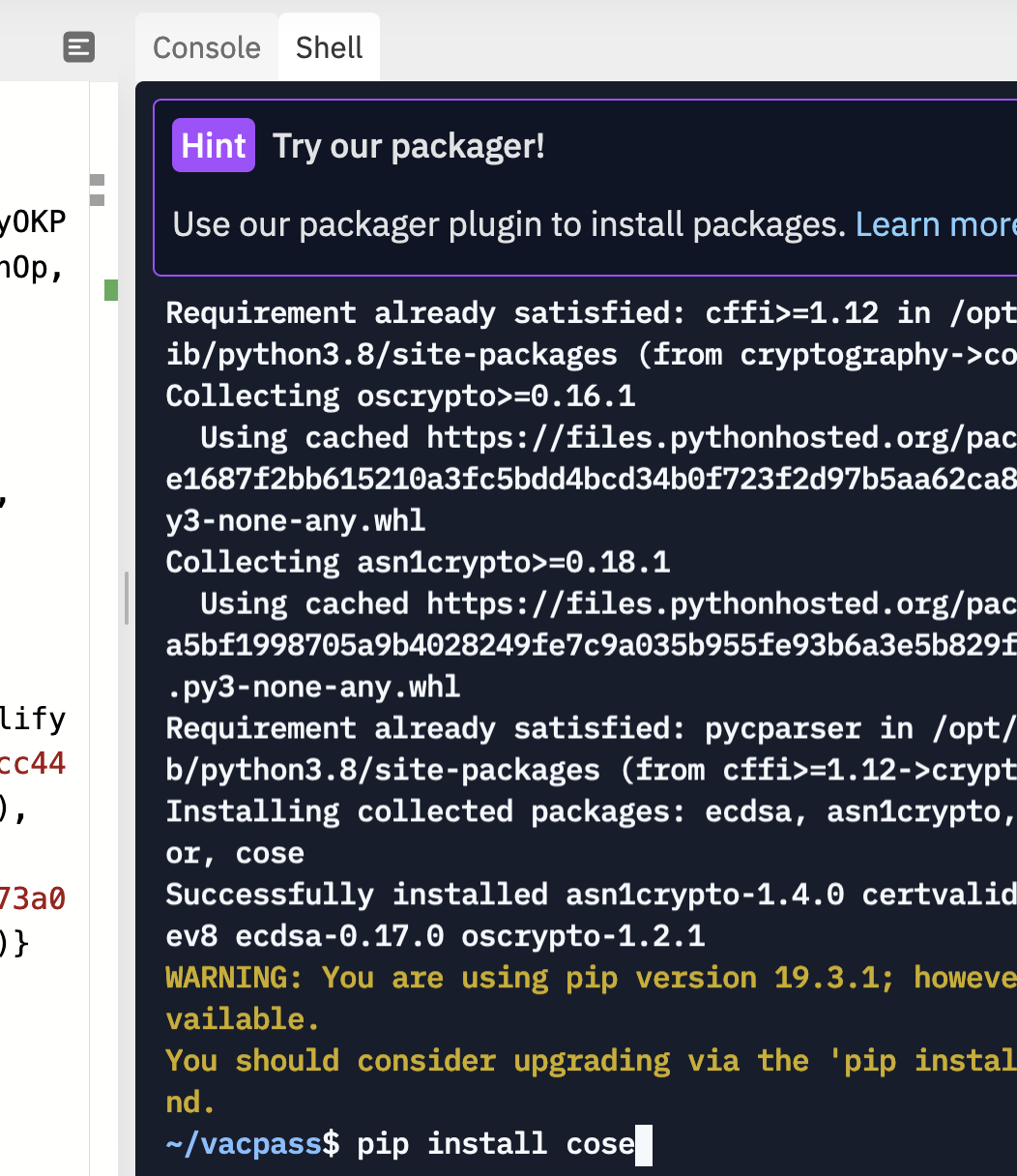
To run the code, you need to pip install cose:
References
[1] Bormann, C., & Hoffman, P. (2020). RFC 8949 Concise Binary Object Representation (CBOR). [here].
[2] Schaad, J. (2017), RFC 8152 – CBOR Object Signing and Encryption (COSE), 2017. [here]
 [
[