Message Authentication Code (MAC)
MACs can be used to authenticate a message, as a key is required to determine the hash value. With this the sender computes the hash with a secret key, and sends to the receiver, where the receive then calculates the hash of the message, and uses the secret key. If the hash received is the same as the computed one, the message has not been tampered with. Typical methods include Gost28147, CMAC, GMAC, Poly1305 and HMAC.
|
Presentation
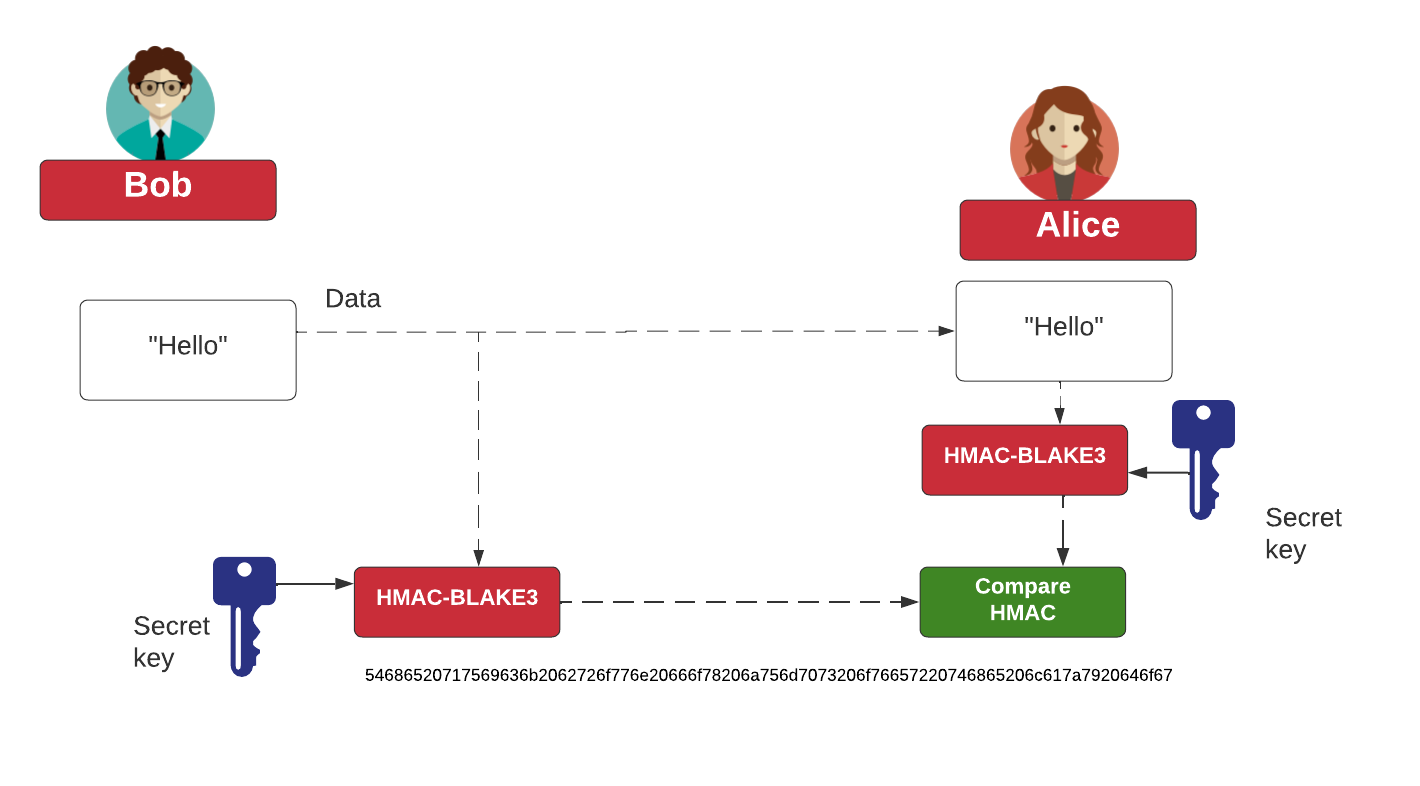
With a MAC, Bob and Alice have the same shared key, and produce a MAC using this shared key, a defined hashing method, and a hash of the message:

 [
[