Tink encryption (MAC)Google has released Tink and which is a multi-language, cross-platform cryptographic library. With OpenSSL we have complex bindings and which were often focused on specific systems, such as for DLLs in Windows systems. Tink is open-source and focuses on creating simple APIs and which should make the infrastructure more portable. In this example we will compute the MAC for a given input string and secret key. For this Bob and Alice have the same shared secret password. When Bob is sending Alice a message, he generates a key based on the password and which uses HMAC and SHA-256 or AES and CMAC. HMAC and CMAC are a keyed hashing methods, and where CMAC uses a symmetric key block cipher (such as AES), whereas HMAC uses a hashing method (such as SHA-256): [Tink Symmetric key][Tink MAC][Tink ECDSA/Ed25519][Tink Hybrid encryption][Tink Envelope encryption][HKDF][Deterministic Authenticated Encryption]: |
Outline
Google Tink is an open source repository for the integration of cryptography methods. It uses best practice in order to reduce risks, and also to simplify code integration. Currently it supports Java, C++ and Objective-C. As Java is well supported on Android devices, the code has already been integrated into a wide range of applications, including Google Pay.
One of the standard methods that we use in cryptography is to sign a message. For this we generate a signing key, and which is kept secret for a range of messages. This could relate to a single conversation between Bob and Alice, or for long-term communications between them.
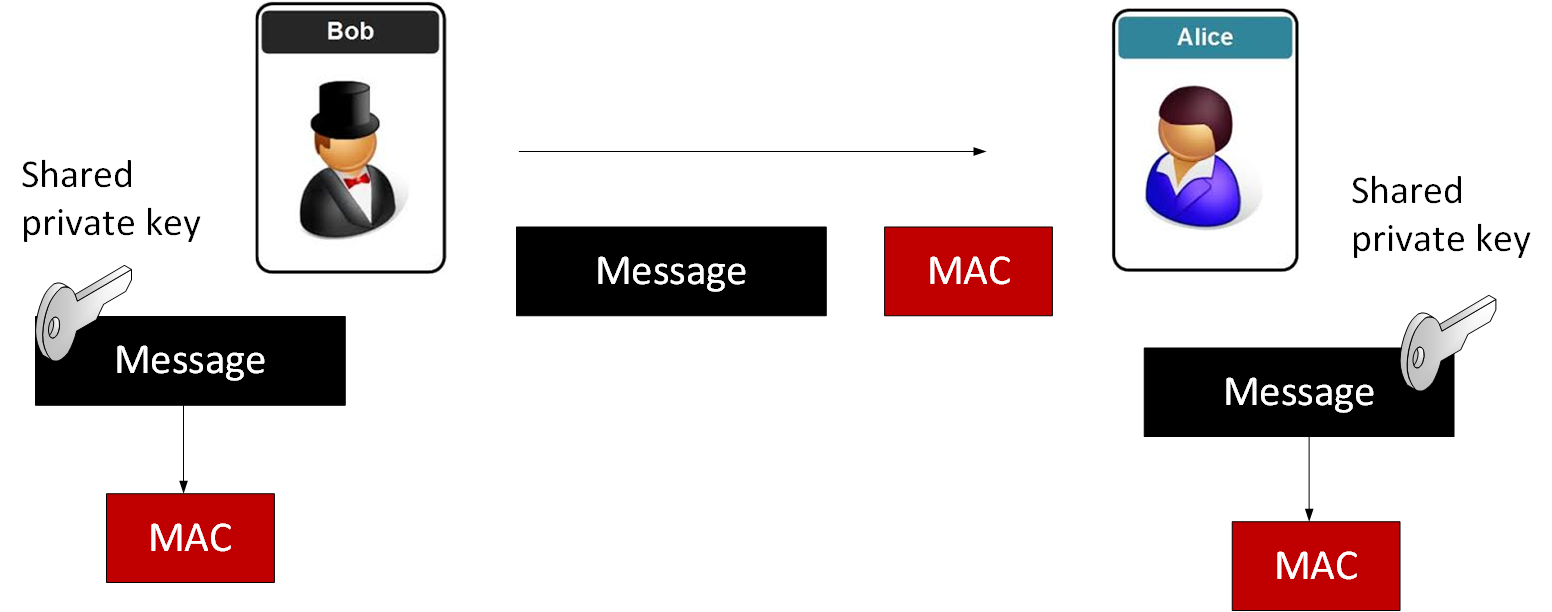
Either Bob or Alice (or both of them) create a shared private key, and then pass it securely. Only Bob and Alice will have this key, and Eve will not be ble to discover it. Every time Bob sends a message to Alice he sends the message with a MAC (Message Authentication Code), and which is the message encrypted with the private key and then produced as a hash code (SHA-256). This method is known has HMAC (Hash-based Message Authentication Code). Alice takes the signing key and checks that she gets the same MAC. If she does, she has checked that it is still Bob who is signing the messages. If it doesn’t tie-up, she assumes that Eve is pretending to be Bob, and discards the message.
Now let’s look at how Google Tink generates MAC codes. For this we generate a new MAC key with getPrimitive() method for MacFactory, and then use the computeMac() to create and verifyMac() to check:
KeysetHandle keysetHandle = KeysetHandle.generateNew(MacKeyTemplates.HMAC_SHA256_128BITTAG);
Mac mac = MacFactory.getPrimitive(keysetHandle);
byte[] tag = mac.computeMac(plaintext.getBytes());
mac.verifyMac(tag,plaintext.getBytes());
A sample run which show the signature for a message of “hello123” for Base-64 and Hex formats:
Text: hello123 MAC: ASJFEIAQEqk9MvGaIsJyKcLiN2iw MAC: 41534A464549415145716B394D76476149734A794B634C694E326977 Valid MAC
The key can also be printed and which shows the symmetric key used (and that we are using HMAC):
Printing out key:
MAC: {
"primaryKeyId": 574951552,
"key": [{
"keyData": {
"typeUrl": "type.googleapis.com/google.crypto.tink.HmacKey",
"keyMaterialType": "SYMMETRIC",
"value": "EgQIAxAQGiAU/p0/1SEV+O1WE/fvQufi7z+rxQ0W6cJeRtgHHtqMQg=="
},
"outputPrefixType": "TINK",
"keyId": 574951552,
"status": "ENABLED"
}]
}
We can see that the encryption key used is “EgQIAxAQGiAU/p0/1SEV+O1WE/fvQufi7z+rxQ0W6cJeRtgHHtqMQg==” and that the format of the HmacKey is defined.
The code is:
package com.helloworld;
import java.util.Base64;
import com.google.crypto.tink.aead.AeadConfig;
import java.security.GeneralSecurityException;
import java.io.ByteArrayOutputStream;
import com.google.crypto.tink.Aead;
import com.google.crypto.tink.KeysetHandle;
import com.google.crypto.tink.Mac;
import com.google.crypto.tink.mac.MacFactory;
import com.google.crypto.tink.mac.MacKeyTemplates;
import com.google.crypto.tink.subtle.Hex;
import com.google.crypto.tink.CleartextKeysetHandle;
import com.google.crypto.tink.JsonKeysetWriter;
public final class HelloWorld {
public static void main(String[] args) throws Exception {
AeadConfig.register();
try {
String plaintext="napier";
int t=1;
if (args.length>0) plaintext=args[0];
if (args.length>1) t=Integer.valueOf(args[1]);
System.out.println("Text:\t"+plaintext);
KeysetHandle keysetHandle = KeysetHandle.generateNew(MacKeyTemplates.HMAC_SHA256_128BITTAG);
if (t==2) {
keysetHandle = KeysetHandle.generateNew(MacKeyTemplates.HMAC_SHA256_256BITTAG);
System.out.println("\nHMAC_SHA256_256BIT TAG");
}
else if (t==3) {
keysetHandle = KeysetHandle.generateNew(MacKeyTemplates.HMAC_SHA512_256BITTAG);
System.out.println("\nHMAC_SHA512_256BIT TAG");
}
else if (t==4) {
keysetHandle = KeysetHandle.generateNew(MacKeyTemplates.HMAC_SHA512_512BITTAG);
System.out.println("\nHMAC_SHA512_512BIT TAG");
}
else if (t==5) {
keysetHandle = KeysetHandle.generateNew(MacKeyTemplates.AES_CMAC);
System.out.println("\nAES/CMAC");
}
else System.out.println("\nHMAC_SHA256_128BIT TAG");
Mac mac = MacFactory.getPrimitive(keysetHandle);
byte[] tag = mac.computeMac(plaintext.getBytes());
byte[] encoded = Base64.getEncoder().encode(tag);
System.out.println("\nMAC (Base64):\t"+ new String(encoded));
System.out.println("MAC (Hex):"+ Hex.encode(encoded));
try {
mac.verifyMac(tag,plaintext.getBytes());
System.out.println("\nValid MAC");
} catch (GeneralSecurityException e) {
System.out.println("In Valid MAC");
}
System.out.println("\nPrinting out key:");
ByteArrayOutputStream outputStream = new ByteArrayOutputStream();
CleartextKeysetHandle.write(keysetHandle, JsonKeysetWriter.withOutputStream(outputStream));
System.out.println(new String(outputStream.toByteArray()));
} catch (GeneralSecurityException e) {
System.out.println(e);
System.exit(1);
}
}
}
With Google Tink we finally get a code based which has now been hacked together over the years (such as with OpenSSL) and which is consistent in its usage and focused on API integration. It is a code based for a modern world.
Presentation
The following is a presentation related to Google Tink [slides]:
 [
[