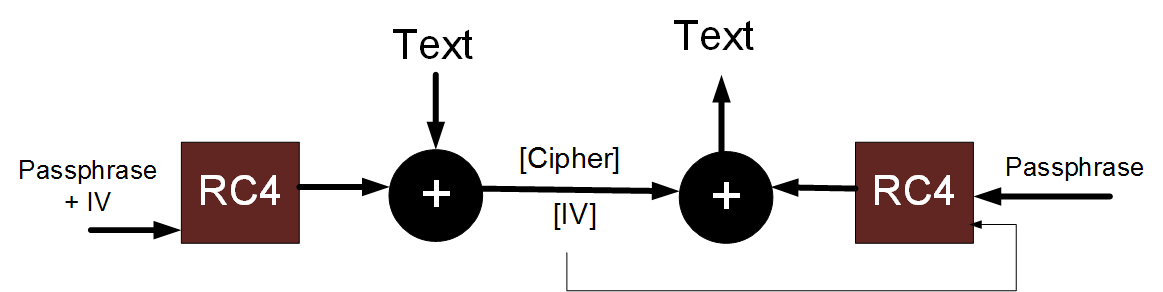
WEP/RC4 Repeating IV ExampleIn encryption we use an IV (Initialisation Vector) to make sure that they encrypted values are different. For example with WEP we transmit: MESS ^ RC4 (Key + IV) where we take the message (MESS) and EX-OR with the RC4 for the key concatenated with the IV value. With WEP, for example, we take the passphrase and the IV and concatenate. Next we create a key using RC4, and EX-OR the data with this. [Theory] The results of the encryption are then:
Now with WEP, we EX-OR the values with the same IV value to get:- MESS1 ^ RC4(KEY+IV) ^ MESS2 ^ RC4(KEY+IV), which will give MESS1 ^ MESS2. Thus if we X-OR the two encrypted values (such as when the IV value repeats):
You will find that the key does not matter in the EX-OR'ed value, as whatever you use as a key will give you the same EX-OR'ed value. So with the same IV value, we get rid of the key, and can just analyse the EX-OR'ed value with frequency analysis. | |||||||
Theory
Sample values:
- Message1 = "hello", Message2 = "hello", Key="fred". Try!. Result is 0000000000
- Message1 = "hello", Message2 = "hello", Key="bert". Try!. Result is 0000000000
- Message1 = "hello", Message2 = "helpo", Key="fred". Try!. Result is 0000001C00
- Message1 = "hello", Message2 = "helpo", Key="bert". Try!. Result is 0000001C00
- Message1 = "The boy", Message2 = "The car", Key="fred". Try!. Result is 00000000010E0B
- Message1 = "The boy", Message2 = "The car", Key="bert". Try!. Result is 00000000010E0B
Theory
In academia we loved WEP, used in the past in Wireless encryption, as it broke every rule of cryptography, and was a great example of what not to do in cryptography. With this the cipher could be replayed back, and could also be copied-and-pasted to create valid messages.
With WEP, in order to produce the cipher stream, we take the passphrase and then concatenate it with a 24-bit IV (Initialisation Vector), and take the RC4 value of it. We then EX-OR the output of this with the data to create the cipher stream, and send the cipher, along with the IV vector. On the other receiver side, we use the passphrase (which is secret and shared on both sides) with the IV and generate the same key, and then simply EX-OR it with the received cipher stream, and the text will be the same of the original data.
Basically with WEP, we waited until the IV value came around again, we EXOR'ed the two cipher streams:
(MESS1 ^ [passphrase + IV)) ^ (MESS2 ^ [passphrase + IV))
when we EXOR the same value together we nullify the EXOR'ing, so we get:
((MESS1 ^ MESS2)
so that the key (and IV) has disappeared, and we don't have the key anymore. The intruder would then just run some frequency analysis, and reveal the original messages.
WEP is thus the king of bad practice, where Intruders eventually got it down to a few hours (by sending lots of ARPs). It had a 24-bit IV value, thus it had 16,777,216, so if we send 1,000 packets a second, then it takes approximately 16,777 seconds to repeat, it will repeat in 279 minutes (or 4.66 hours).
WEP was one of the greatest disasters in cryptography and broke virtually every rule. As it's core was the simple EX-OR'ing of the bit stream, using an IV and passphrase. Once the IV repeated, it was easy to determine the original messages. If you're interested, here are some other weaknesses in cryptography:
Link [
[