Diffie-Hellman Key exchange (Discrete Logs)
Key exchange is a way for Bob and Alice to communicate and for them to agree on a shared secret. The original method defined uses discrete logarithms (Diffie-Hellman). With the Diffie-Hellman method, Alice generates \(a\) and shares \(A=g^a \pmod p\) with Bob. Bob generates \(b\) and shares \(B=g^b \pmod p\). Alice raises \(B\) to the power of \(a\), and Bob raises \(A\) to the power of \(b\). They should both end up with the same secret: \(K=g^{ab} \pmod p\).
|
Outline
The Diffie-Hellman (DH) method is perhaps one of the greatest inventions in Cybersecurity, and was created by Whitfield Diffie and Marty Hellman. With the DH method, Bob creates a random value (\(b\)) and Alice also creates a random value (\(a\)). Next Bob computes \(B=g^b \pmod p\) and sends it to Alice. Alice computes \(A=g^a \pmod p\) and sends this to Bob. Bob raises the value of \(A\) to the power of \(b\) and takes \(\pmod p\), and Alice raises \(B\) to the power of \(a\) and takes \(\pmod p\). In the end, they will have the same shared value: \(g^{ab} \pmod p\). This can then be used to derive an encryption key that they can use for a secure tunnel (Figure 1). Overall, \(p\) is the large prime number, and also known as the shared modulus between Bob and Alice.
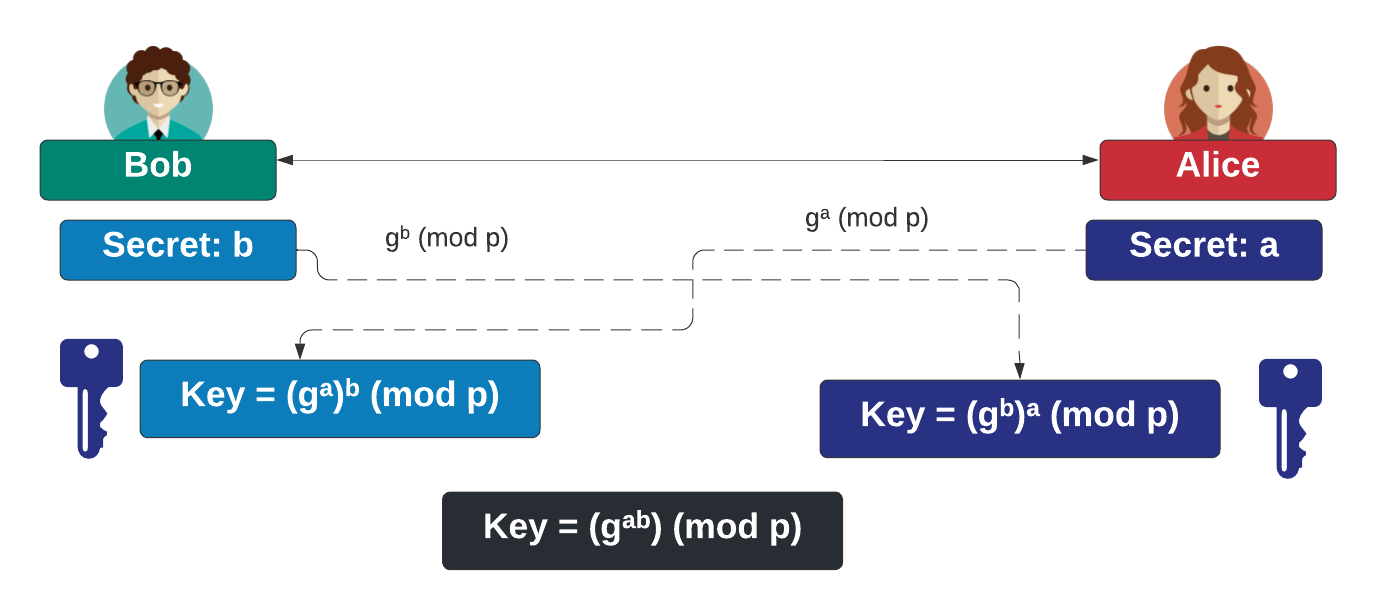
Figure 1
Presentation

 [
[